The digital landscape is currently witnessing a paradigm shift in the methodology of cybercrime as traditional “spray and pray” tactics give way to sophisticated, data-driven operations. Modern phishing has evolved from generic, poorly written emails into a professionalized enterprise where attackers function like legitimate business owners with organized hierarchies and refined strategies. By leveraging Artificial Intelligence and an abundance of leaked personal data, scammers have moved toward hyper-targeted manipulation, making it increasingly difficult for the average user to distinguish a fraudulent message from a legitimate one. This evolution reflects a broader trend where cybercriminals utilize large language models to refine their messaging and eliminate common red flags like grammatical errors or awkward phrasing. The transition from broad-spectrum attacks to highly specific engagements represents a maturation of the illicit digital economy, where the primary goal is maximizing conversion rates through psychological exploitation. As these actors adopt the strategies of modern marketing firms, they analyze behavior to ensure every interaction feels authentic.
The Data Ecosystem: Powering Personalized Attacks
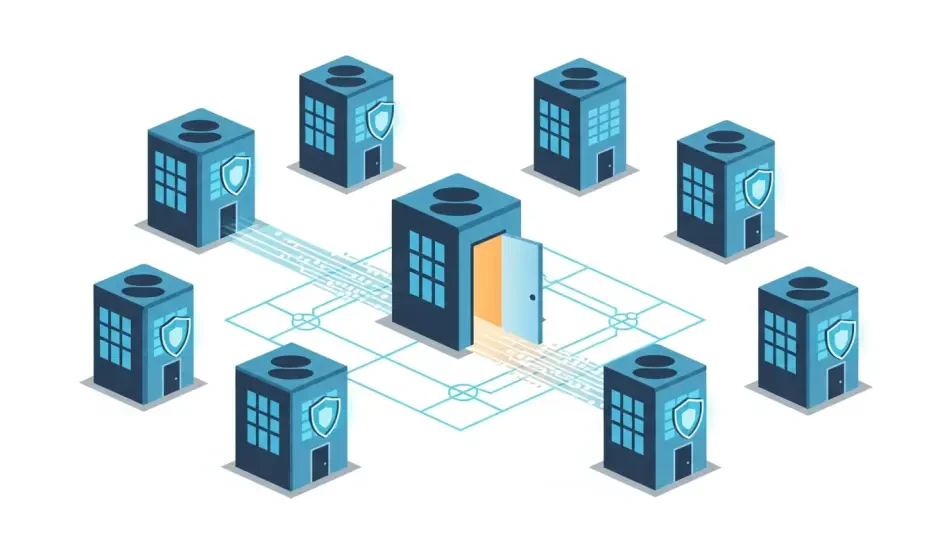
Personalized scams do not emerge in a vacuum; they are fueled by an extensive ecosystem of both illicit and public data that is more accessible than ever before. Scammers aggregate information from massive corporate breaches and previous successful phishing attempts, but they also harvest details from legitimate sources like marketing databases and social media footprints. By analyzing public posts, hackers can discern a target’s interests, travel plans, and professional affiliations, allowing them to transform a “cold contact” into a “warm lead” that feels like a continuation of a trusted conversation. This synthesis of data enables a level of precision that was previously impossible for low-level actors to achieve. The integration of stolen credentials with publicly available lifestyle information creates a comprehensive profile of the victim, making the subsequent attack feel naturally integrated into their daily digital routine. This data-driven foundation is what allows modern phishing to bypass traditional filters that look for generic patterns and broad indicators of compromise.
This wealth of information allows attackers to categorize their efforts into different tiers of sophistication, starting with geographic targeting that relies on regional familiarity. Using simple identifiers like a phone area code or a registered home address, scammers can ground a lie in a victim’s local reality, such as sending a text about unpaid tolls that mentions a specific regional authority. By moving away from generic messages and referencing local entities like the Department of Motor Vehicles or specific bridge authorities, the attacker effectively bypasses the natural skepticism that usually protects users from broader, non-specific scams. These localized attacks are often the first point of entry, testing the victim’s responsiveness before moving toward more complex schemes. The use of regional nuances, such as referencing a local weather event or a specific neighborhood infrastructure project, adds a layer of superficial legitimacy that encourages the recipient to click a link or provide sensitive information without the usual hesitation associated with unknown senders.
High-Level Manipulation: Lifestyle and Behavioral Exploitation
At a more advanced level, scammers utilize “fill-in-the-blank” templates powered by leaked databases containing full names, physical addresses, and specific service provider details. These messages often take the form of official government or corporate notices, creating a psychological impact that triggers a sense of urgency or fear regarding legal registrations or financial penalties. When a message addresses a victim by their full name and references a service they actually use, the perceived legitimacy of the threat increases exponentially, leading to higher conversion rates for the criminal. This method exploits the human tendency to trust formal communications that contain accurate personal identifiers. The psychological pressure applied in these scenarios is carefully calibrated to discourage the victim from taking the time to verify the sender’s identity. By framing the communication as a time-sensitive matter requiring immediate action, the attacker forces a reactive decision-making process that favors the success of the scam over the security of the individual.
The most insidious form of modern phishing is the hyperpersonalized or “lifestyle” scam, which involves deep research into a target’s habits and emotional state. Scammers might exploit health interests by sending deceptive links to fake pharmacies or engage in long-term “pig butchering” schemes where they build rapport over weeks or months. By weaving personal details like a victim’s alma mater or shared hobbies into the narrative, the attacker establishes a false sense of intimacy, which often concludes with significant financial extortion or emotional blackmail. These attacks are particularly dangerous because they rely on the slow erosion of boundaries through consistent, personalized engagement. The attacker often assumes a persona that mirrors the victim’s values or professional background, making the eventual request for money or data seem like a natural extension of a burgeoning relationship. This level of dedication to a single target demonstrates the shift toward high-value, long-term fraud over the high-volume, low-effort tactics of the previous decade.
The Role of Artificial Intelligence: Scaling Modern Scams
Artificial Intelligence serves as the primary catalyst for this surge in personalization, democratizing high-level scamming for low-skill actors across the globe. AI tools allow criminals to generate natural-sounding prose in any language, removing the grammatical errors and syntax issues that once served as red flags for phishing. Furthermore, AI can process massive datasets instantly to identify cultural markers and regional nuances, drastically reducing the “cost of production” for a scam while increasing its profitability through higher success rates. The ability to automate the creation of unique, personalized messages means that attackers can now launch thousands of hyper-targeted campaigns simultaneously. This scalability has transformed phishing from a manual craft into an automated industrial process. Large language models are also being used to simulate real-time conversations, allowing bots to interact with victims in a way that feels human and responsive, further lowering the barrier for entry for criminals who may not speak the victim’s native language fluently.
This technological evolution has expanded the demographic profile of potential victims, as hyperpersonalized scams are increasingly effective against tech-savvy adults who might have felt immune to older tactics. The psychological grooming involved in these modern schemes often results in a sense of shame that prevents victims from reporting the crime once they realize they have been deceived. This silence creates a protective barrier for scammers, allowing them to continue their operations without interference from law enforcement or public awareness campaigns. Because the scams are so tailored, victims often feel a personal sense of failure, not realizing they were targeted by a sophisticated machine-learning algorithm designed to exploit specific vulnerabilities. The broad reach of these AI-driven campaigns ensures that no segment of the population is truly safe, as the software can adapt its approach based on the specific digital footprint of any individual. This adaptability makes modern phishing a constantly moving target for cybersecurity professionals and everyday users.
Immediate Response: Financial and Legal Remediation
If an individual falls victim to these sophisticated schemes, security experts emphasize the importance of immediate damage control over emotional reactions. The first priority is financial intervention, which involves contacting banks or credit card issuers to freeze accounts and dispute any fraudulent charges that may have appeared. Taking swift action can prevent further unauthorized withdrawals and provides a formal record of the theft, which is essential for any subsequent legal or insurance claims. In addition to freezing accounts, it is necessary to change passwords for all sensitive services, especially if the scam involved any form of credential harvesting. Victims should also review their account settings to ensure that no secondary emails or unauthorized recovery methods were added by the attacker. This initial response phase is critical for containing the breach and preventing a single compromised account from leading to a total financial loss. Documenting every step of the communication with financial institutions provides a necessary trail for investigators.
Beyond banking, victims must address the long-term risks associated with identity theft by implementing a “security freeze” on their credit reports to prevent future abuse. This prevents scammers from using stolen Social Security numbers or sensitive identification to open new lines of credit in the victim’s name. Utilizing resources like the federal consumer advice pages provides a structured path for recovery and helps law enforcement track emerging patterns, which is vital for dismantling the infrastructure that supports these AI-driven criminal enterprises. Reporting the incident also helps in the collective defense against these threats, as the data provided can be used to update spam filters and security protocols for the general public. While the immediate loss might be financial, the long-term risk of identity exploitation requires a persistent and methodical approach to remediation. Staying vigilant for months following an attack is often necessary, as stolen data is frequently sold and reused by different criminal groups in various secondary fraudulent schemes.
Proactive Defense: Maintaining Digital Security Hygiene
The defense against personalized phishing required a multi-layered approach that combined technical tools with disciplined behavioral changes to ensure long-term safety. Users maintained updated antivirus software and utilized password managers to ensure that a breach at one service provider did not grant access to their entire digital life. Keeping operating systems and browsers updated was equally critical, as these updates frequently included patches for the specific vulnerabilities that scammers exploited to gain a foothold in a victim’s device. Implementing multi-factor authentication across all sensitive accounts became a non-negotiable standard for preventing unauthorized access even when credentials were compromised. These technical layers functioned as the primary barrier against the automated portions of an attack, forcing criminals to invest more time and effort into each attempt. By automating the defensive side of the equation, individuals were able to focus their attention on the more nuanced psychological aspects of modern social engineering and deceptive digital communications.
Ultimately, the “human firewall” remained the most important line of defense in an era of AI-driven deception and sophisticated manipulation. This involved a mindful approach to digital communication, such as questioning any “official” message that demanded urgent action or contained unsolicited links. By limiting the amount of personal information shared on public social media platforms and maintaining a healthy level of skepticism toward unexpected digital interactions, individuals better protected themselves against the evolving tactics of modern cybercriminals. Educational initiatives focused on identifying the psychological triggers used by scammers, such as the creation of false urgency or the exploitation of authority. As AI continued to evolve, the public responded by adopting more rigorous verification methods, such as contacting organizations directly through official channels rather than clicking on provided links. This proactive stance, combined with robust technical safeguards, formed a resilient defense that empowered users to navigate the internet with greater confidence and significantly reduced the success rate of malicious actors.