The rapid evolution of the United Arab Emirates into a global technology powerhouse has fundamentally altered the traditional parameters of national sovereignty and border protection. As the nation deepens its reliance on interconnected digital systems, the concept of national security has expanded to include the integrity of the invisible networks that manage everything from high-speed finance to municipal water systems. This shift has necessitated a move away from reactive security measures toward a sophisticated, institutionalized framework designed to safeguard the economic and social stability of the country. By prioritizing digital sovereignty, the leadership has begun the process of constructing a comprehensive digital fortress. This initiative is not merely about defensive technology but represents a fundamental reimagining of how a modern state protects its interests against anonymous, borderless adversaries who operate in the shadows of the global internet.
Navigating a Complex Digital Battlefield
Evolution: The Nature of Modern Cyber Risks
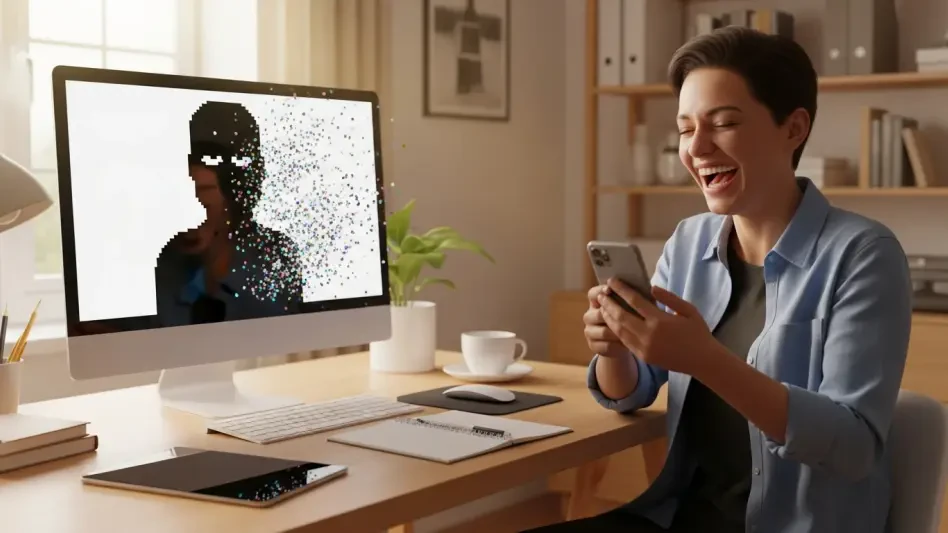
Modern cyber threats present a unique set of challenges that differ significantly from traditional physical security risks due to their shapeless and often untraceable nature. In the current landscape, attackers leverage sophisticated tools such as artificial intelligence and deepfake technology to conduct operations that can bypass conventional security protocols with alarming ease. The primary difficulty remains the attribution problem, as hackers, ranging from independent criminal syndicates to state-sponsored actors, utilize advanced obfuscation techniques to mask their origins and intentions. This lack of a clear physical presence means that the UAE must maintain a state of constant, proactive monitoring rather than waiting for a breach to occur. Consequently, the focus has shifted toward high-level cyber hygiene and the deployment of predictive analytics to identify potential vulnerabilities before they can be exploited by hostile entities seeking to disrupt the national digital ecosystem.
Furthermore, the rise of the ransomware-as-a-service model has lowered the barrier to entry for digital criminals, resulting in a higher frequency of automated and persistent attacks. These operations often target the supply chains that support critical government functions, making it difficult to isolate a single point of failure. The UAE’s response involves a multi-layered defense strategy that treats every connection point as a potential risk, ensuring that no single system is left unprotected. By understanding that the battlefield is now composed of code and data packets, the nation has invested heavily in developing indigenous capabilities to counter these emerging threats. This approach requires not only technological superiority but also a deep understanding of the psychological tactics used in social engineering and phishing campaigns, which remain a primary vector for initial network intrusions across both public and private sectors.
Strategic Risks: The UAE as a High-Value Target
The success of the United Arab Emirates as a premier global hub for finance, aviation, energy, and logistics inherently makes it a primary target for international cybercriminal activity. Because the economy is so deeply integrated with global markets, a single localized breach in a critical sector could potentially trigger a cascading effect that disrupts international supply chains and erodes investor confidence. For instance, the energy sector, which is central to global energy security, requires specialized protection to prevent any interference with oil and gas production or distribution networks. Similarly, the aviation industry, led by global carriers like Emirates and Etihad, relies on complex digital frameworks for flight operations and passenger safety, making it a high-stakes environment for cybersecurity professionals. The interconnectedness of these sectors means that resilience is not just a local concern but a vital component of global economic stability.
In addition to traditional industries, the rapid expansion of smart-city initiatives in Dubai and Abu Dhabi has introduced thousands of new digital interfaces that must be secured against unauthorized access. Every smart meter, traffic control system, and digital government service represents a potential entry point for an attacker if not properly managed. This high density of digital touchpoints puts a significant amount of personal and sensitive data at risk, requiring a robust defense-in-depth strategy. To mitigate these risks, the UAE has implemented comprehensive data sovereignty rules and localized cloud storage requirements to ensure that critical information remains within protected jurisdictions. The focus on resilience ensures that even if a system is compromised, the nation possesses the redundant infrastructure and recovery protocols necessary to maintain essential services and minimize the impact on the daily lives of its residents.
Building a Unified Defense Framework
Command: Institutional Leadership and Regulatory Power
Centralized leadership serves as the foundational pillar of the UAE’s cyber defense strategy, a role that was solidified with the establishment of the UAE Cybersecurity Council. Under the direction of specialized leadership, this council has moved beyond incident management to become the primary architect of national digital policy. By creating a unified framework that bridges the gap between federal agencies and local municipal entities, the council ensures that the nation speaks with one voice when addressing digital threats. This centralized approach allows for the rapid dissemination of threat intelligence and the coordination of large-scale defensive maneuvers that would be impossible in a fragmented system. The council also facilitates a unique environment of public-private cooperation, encouraging major corporations to share data on emerging threats in exchange for real-time government support and technical guidance.
Complementing this institutional leadership is a rigorous modern legal framework, most notably Federal Decree Law No. 34 of 2021, which provides the judicial system with the tools needed to prosecute a wide array of digital crimes. This legislation covers everything from identity theft and online extortion to the unauthorized access of sensitive state databases, ensuring that there are clear and severe consequences for those who threaten the nation’s digital integrity. Beyond general criminal law, the UAE has introduced sector-specific regulations that mandate high security standards for the banking, healthcare, and telecommunications industries. These regulations require organizations to adhere to strict cloud compliance and data protection protocols, effectively raising the collective security floor for the entire country. By codifying these requirements into law, the government has ensured that cybersecurity is treated as a non-negotiable component of doing business within the national borders.
Governance: Sector-Specific Compliance and Standards
The regulatory landscape in the UAE is designed to be both flexible and rigorous, allowing it to adapt to the specific technological needs of different economic sectors while maintaining a high baseline of security. For example, the financial sector is subject to specialized protocols that mandate the use of advanced encryption and multi-factor authentication for all transactions to prevent fraud and money laundering. These standards are not merely suggestions but are enforced through regular audits and compliance checks conducted by the relevant regulatory bodies. This creates a culture of accountability where businesses are required to prioritize the safety of their customers’ data as a core operational requirement. By aligning local regulations with international standards like ISO and NIST, the UAE ensures that its domestic companies can operate seamlessly and securely within the global digital economy.
Moreover, the government has prioritized the security of the telecommunications infrastructure, recognizing it as the nervous system of the digital nation. Regulations in this sector focus on preventing unauthorized interceptions and ensuring the physical and logical security of the fiber-optic networks and satellite links that connect the UAE to the rest of the world. Specialized data protection laws also govern how cloud service providers operate, requiring them to implement transparent data handling practices and robust disaster recovery plans. These measures are designed to protect the privacy of individuals while providing the government with the necessary oversight to detect and mitigate large-scale threats. This comprehensive regulatory approach ensures that every participant in the digital economy contributes to the overall resilience of the nation, creating a shared defense mechanism that is greater than the sum of its individual parts.
Implementing Technical and Social Safeguards
Defense: Frontline Countermeasures and Technical Readiness
On the technical frontline, the UAE Computer Emergency Response Team, known as aeCERT, acts as the primary defense mechanism against active vulnerabilities and emerging malware. This specialized unit provides 24-hour monitoring of the national digital space, offering immediate assistance to government agencies and critical infrastructure operators during the early stages of a cyberattack. One of the core strategies adopted under this technical framework is the implementation of Zero-Trust security models, which operate on the principle that no user or device should be automatically trusted, regardless of whether they are inside or outside the network perimeter. This approach requires continuous verification through sophisticated identity management systems, significantly reducing the risk of lateral movement by an attacker who has managed to gain an initial foothold in a system.
In addition to defensive architectures, the UAE has invested in advanced encryption technologies to secure sensitive state communications and commercial data from prying eyes. These technical safeguards are regularly tested through large-scale simulation exercises that mimic the tactics of state-sponsored actors and professional criminal organizations. These drills are essential for identifying hidden weaknesses in the national infrastructure and for training technical staff to respond under high-pressure scenarios. By integrating threat intelligence from global partners and technology firms, the nation stays informed about the latest malware variants and exploit kits before they reach local networks. This proactive technical readiness ensures that the UAE is not just reacting to the threats of the past but is actively preparing for the complex challenges posed by future technological developments in artificial intelligence and quantum computing.
Awareness: The Human Element and Public Education
The UAE has recognized that even the most advanced technical defenses can be undermined by human error, which is why public awareness has become a cornerstone of national security. Under the guidance of the Cybersecurity Council, the government has launched extensive educational campaigns designed to teach cyber hygiene to all segments of society, from primary school students to corporate executives. These programs focus on identifying common social engineering tactics, such as phishing emails and fraudulent phone calls, which are often used to steal login credentials or install malicious software. By framing cybersecurity as a shared social responsibility, the government aims to empower every citizen to act as a sentry in the nation’s digital defense. This cultural shift ensures that individuals are more skeptical of unsolicited digital interactions and more diligent in protecting their personal information.
Furthermore, these educational initiatives extend into the professional sphere, where specialized training is provided to employees in critical sectors such as energy and healthcare. These workers are trained to recognize the signs of a potential breach and are taught the proper protocols for reporting suspicious activity to the relevant authorities. The government also utilizes digital platforms to issue real-time alerts about new fraudulent schemes, keeping the public informed and vigilant against evolving threats. This focus on the human element recognizes that a well-informed population is one of the most effective deterrents against cybercrime. By building a culture of vigilance, the UAE has created a resilient social fabric that complements its technical and legal frameworks, ensuring that the nation’s digital transformation is supported by a population that understands the importance of maintaining a secure and trustworthy online environment.
Sector-Specific Resilience and Future Growth
Protection: Specialized Security for Vital Industries
The resilience strategy of the United Arab Emirates is characterized by its tailored approach to the unique needs of different critical industries, ensuring that each sector has the specific tools required to face its particular threats. For example, the Abu Dhabi National Oil Company, ADNOC, has pioneered the use of dedicated cybersecurity operations centers that use machine learning to monitor industrial control systems for any signs of tampering. These centers are designed to protect the physical hardware that manages energy production, ensuring that a digital intrusion cannot lead to physical damage or environmental hazards. Similarly, the aviation sector has aligned its digital protocols with international safety standards, creating a seamless security environment that protects both operational data and passenger privacy across global flight networks.
In the realm of digital government, agencies such as the Abu Dhabi Digital Authority have established rigorous guidelines for the use of cloud systems, ensuring that smart-city projects are built on a secure and scalable foundation. These guidelines include requirements for automated threat detection and the use of sovereign cloud solutions that keep sensitive government data within the country’s borders. This sectoral approach also extends to the logistics and maritime industries, where port operators use advanced tracking and security systems to manage the flow of goods through some of the world’s busiest shipping lanes. By providing specialized support and clear regulatory standards for these vital industries, the UAE has ensured that the pillars of its economy remain stable and secure, even in the face of targeted and highly sophisticated digital attacks.
Innovation: Security as a Foundation for Progress
The strategic evolution of the United Arab Emirates during this period demonstrated that security was not a static destination but a continuous process of adaptation and foresight. Actionable steps taken by the leadership focused on integrating cybersecurity into the very fabric of national innovation, ensuring that new developments in artificial intelligence and financial technology were secure by design. The government successfully moved beyond the reactive measures of the past by fostering a robust ecosystem where academic research, private sector expertise, and state authority worked in harmony. This collaborative model provided a clear blueprint for other nations seeking to navigate the complexities of the digital age, proving that economic growth and national security were mutually reinforcing goals.
Future considerations for the nation involved the continuous refinement of the three pillars of institutional coordination, legal robustness, and social responsibility. It was concluded that the ability to remain a leader in the global digital economy depended on the constant upgrading of technical defenses and the ongoing education of the workforce. The transition to a proactive security posture effectively neutralized many of the risks associated with hyper-connectivity, allowing the UAE to embrace emerging technologies with confidence. By treating every digital connection as a vital link in a national chain of trust, the country established itself as a resilient and reliable node in the global network. These efforts ensured that the digital future remained a space of opportunity rather than a source of vulnerability, marking a successful chapter in the nation’s journey toward total digital sovereignty.