The terrifying sight of a sudden government alert flashing across a smartphone screen can paralyze the senses, making even the most tech-savvy individual prone to reactive decisions. Capitalizing on this raw vulnerability, a sophisticated wave of “quishing” attacks—phishing via QR codes—has emerged to exploit heightened geopolitical anxieties regarding conflicts in the Middle East. By blending psychological warfare with modern digital evasion, threat actors are successfully bypassing traditional security layers to infiltrate secure corporate and personal accounts.
The High-Stakes Psychology of Geopolitical Fear
Cybercriminals have pivoted away from obvious suspicious links, turning instead toward the perceived legitimacy of QR codes. By weaponizing the real-world tension between Iran, Israel, and the United States, these attackers ensure their messages are not just seen, but felt. When a person receives a notification that suggests a potential threat to their physical safety, the brain often enters a “fight or flight” mode that overrides logical skepticism.
The danger lies in this impulsive decision-making process, which occurs when individuals believe they are in a national emergency. During these high-stress moments, the priority shifts from digital hygiene to physical survival. Attackers know that a victim who is checking for missile trajectories is far less likely to scrutinize the sender’s email headers or the destination of a scanned image.
Anatomy of the Missile Alert Quishing Campaign
The current campaign utilizes a meticulously spoofed “Ministry of Interior and Civil Defense” sender address to establish immediate authority. The emails are framed as urgent “Public Safety Advisories,” designed to look identical to official government communications. By using alarmist instructions to “seek immediate shelter” and “view emergency protocols,” the attackers create a sense of frantic urgency that demands immediate interaction.
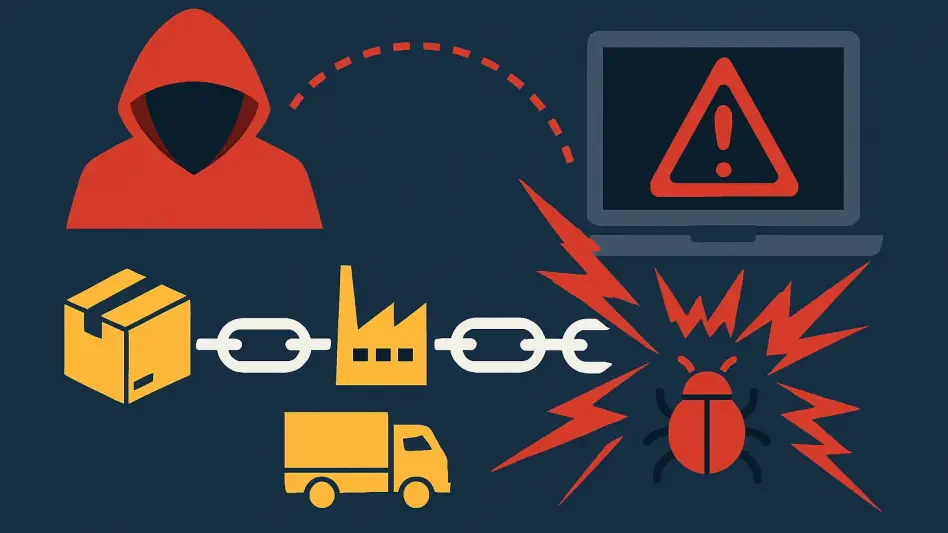
Traditional email security filters often fail to intercept these malicious payloads because the threat is embedded within an image file. While modern scanners are proficient at detecting malicious URLs or dangerous attachments, a QR code is simply a graphic until a human interacts with it. This technical blind spot allows the fraudulent message to land directly in the primary inbox, where it carries the weight of a legitimate state warning.
The Multi-Stage Deception Process
The deception does not end with the initial scan; instead, it transitions into a structured psychological trap. Upon scanning the code, victims are redirected to a fraudulent “human check” page, often featuring a captcha or a verification prompt. This intermediate step is a clever trick designed to build a false sense of security, making the user believe they are entering a protected, official government portal.
Once the “verification” is complete, the user is funneled to a pixel-perfect replica of a Microsoft login page. This transition exploits the ubiquity of the Microsoft brand, leading victims to believe that their identity must be verified through their corporate or personal account to access the “civil defense” files. By the time the user enters their credentials, the psychological momentum of the emergency has carried them past any remaining red flags.
Expert Insights on Tactical Evasion and Social Engineering
Research from the Cofense Phishing Defense Center indicates that quishing is evolving into a preferred method for high-value credential harvesting. The strategic timing of these attacks is no coincidence; they are frequently launched during breaking news cycles when public fear is at its peak. This alignment with global events ensures that the scam feels relevant and timely, rather than like a random piece of spam.
Security experts note that psychological manipulation is now becoming more effective than technical exploits. As software patches close traditional vulnerabilities, the “human operating system” remains the most exploitable target. The blend of a high-stress environment with a novel delivery mechanism like the QR code creates a perfect storm for successful account takeovers across various industries.
Defending Against Emergency-Themed Cyber Threats
The golden rule for navigating this landscape is to never scan unsolicited QR codes received through unexpected emails, regardless of how official they appear. Legitimate government agencies rarely use email-based QR codes to distribute critical safety information. If an alert seems real, the safest course of action was to verify the data by navigating directly to a known government website or using an official emergency response application.
To mitigate the fallout from harvested credentials, implementing robust multi-factor authentication (MFA) became a mandatory baseline. Organizations also prioritized behavioral training that specifically addressed the rising threat of quishing. By shifting focus toward verifying the source of the communication rather than reacting to the content of the message, users established a more resilient defense against the weaponization of global fear.