The systematic dismantling of a global medical giant’s digital footprint within hours has redefined the stakes of digital safety in the healthcare sector. As the MedTech industry moves toward an era of total connectivity, the traditional boundaries between hospital hardware and global software networks have dissolved. This shift has transformed medical devices from standalone tools into integrated nodes within a vast, interdependent ecosystem. While this evolution has drastically improved patient outcomes and surgical precision, it has simultaneously introduced unprecedented systemic risks. The recent disruption of a major American orthopedic leader serves as a stark reminder that the modern medical infrastructure is no longer just a target for common criminals but a frontline in geopolitical conflict.
The Evolution and Integration of MedTech Infrastructure
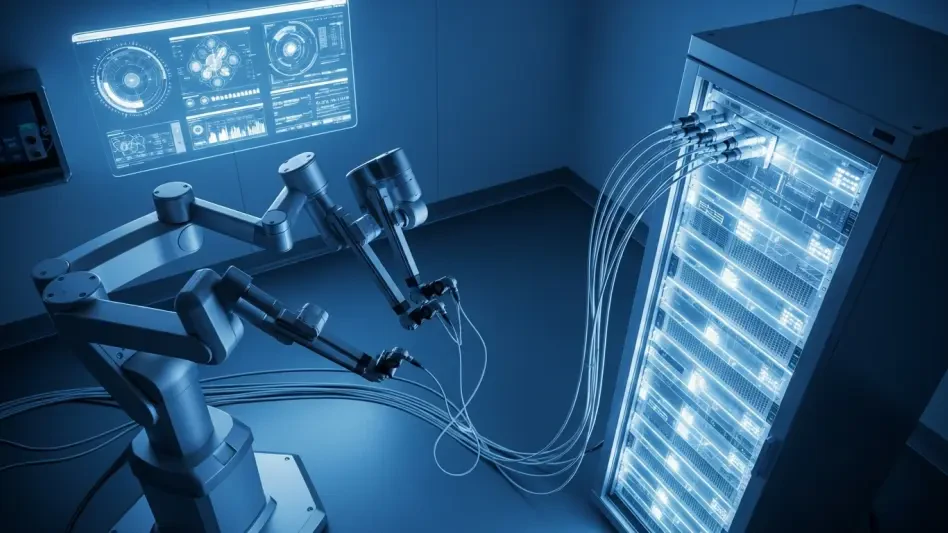
The transition from mechanical hospital equipment to digital-first medical technology began as an effort to streamline clinical workflows and enhance diagnostic accuracy. At its core, modern MedTech relies on the integration of specialized hardware with standardized operating systems, allowing for seamless data exchange across global networks. This convergence allows a surgeon in one country to utilize robotic tools developed and updated in another, creating a truly borderless healthcare environment. However, this level of integration requires a foundation of constant connectivity, making the reliability of the underlying digital architecture as critical as the physical tools themselves.
This technological landscape is characterized by its reliance on enterprise-level software environments, often built upon ubiquitous platforms like Microsoft Windows. By utilizing these common frameworks, medical companies can deploy updates quickly and manage thousands of devices across multiple continents. The context of this evolution is rooted in the demand for real-time analytics and remote monitoring, which have become essential for maintaining high standards of care. Yet, the very standardization that enables global scalability also creates a uniform attack surface, where a single vulnerability can echo through the entire supply chain.
Critical Components of Modern Medical Digital Environments
Cloud-Based Healthcare Ecosystems: A Centralized Vulnerability
Cloud integration has become the central nervous system of modern healthcare, hosting everything from patient records to the software licenses required to operate surgical robots. These ecosystems function by centralizing data processing and storage, which enhances performance by allowing devices to offload heavy computational tasks to high-powered remote servers. This significance cannot be overstated, as it enables the deployment of complex medical applications in resource-limited settings. However, this centralization creates a massive dependency; if the cloud environment is compromised, every connected device loses its primary source of intelligence and operational capacity.
Endpoint Device Management and Remote Access: The New Battlefield
Endpoint management involves the technical oversight of every laptop, tablet, and smartphone used by a workforce to interact with corporate and clinical data. In a globalized company, these devices are controlled through centralized management protocols that allow IT departments to push security patches or, in extreme cases, wipe data to prevent theft. While these features are designed for protection, they represent a dual-use technology. When state-linked actors gain control of these management tools, they can weaponize the security features against the organization, turning a protective “remote wipe” command into a tool for mass digital destruction across an entire fleet of hardware.
Emerging Trends in State-Linked Cyber Operations
The landscape of cyber threats has shifted from opportunistic ransomware attacks toward sophisticated, state-sponsored operations aimed at systemic destabilization. Groups like Handala, which researchers link to national intelligence agencies, have moved beyond simple data encryption for profit. Their current strategy focuses on the total erasure of digital assets and the disruption of critical infrastructure to achieve political or geopolitical objectives. This trend highlights a move toward “wiper” attacks that prioritize chaos and operational paralysis over financial gain, signaling a more aggressive stance in the global digital arena.
Real-World Applications and Global Network Dependencies
Medical technology is now deeply embedded in the daily operations of hospitals, clinics, and research facilities worldwide. From advanced orthopedic implants to surgical robotics, the global network of dependencies ensures that a disruption in one region can halt surgeries in dozens of others. This is particularly evident in the medical equipment sector, where the supply chain for parts and software updates is often centralized. A collapse in the digital backbone of a major provider affects the delivery of essential tools to thousands of global partners, demonstrating how modern healthcare is inextricably linked to the stability of private corporate networks.
Technical Vulnerabilities and Regulatory Hurdles
One of the primary technical hurdles facing the industry is the aging nature of many medical devices, which were not originally designed with modern cybersecurity in mind. These “legacy” systems often run on outdated software that is difficult to patch without disrupting their medical certifications. Furthermore, the regulatory environment is struggling to keep pace with the speed of cyber innovation. Compliance requirements often vary by region, creating a fragmented landscape that makes it difficult for companies to implement a unified security standard. Efforts are ongoing to develop more resilient, “secure-by-design” frameworks, but these face significant market obstacles due to the high costs of implementation.
The Future of Resilient Healthcare Infrastructure
Looking forward, the industry is likely to pivot toward decentralized security models and autonomous threat detection systems. Future developments will focus on creating air-gapped backups for critical surgical data and implementing “Zero Trust” architectures where every device must constantly verify its credentials. Breakthroughs in AI-driven monitoring could allow systems to identify and isolate malicious commands before they can propagate through the network. The long-term impact will be a move away from total centralization, as organizations recognize that resilience requires a balance between global connectivity and localized operational independence.
Assessment of the MedTech Cybersecurity Landscape
The recent events involving global medical leaders proved that digital security is no longer an auxiliary concern but a core component of patient safety. Industry stakeholders recognized that the reliance on centralized management tools created a dangerous single point of failure. In response, many organizations shifted their investment strategies toward redundant hardware and decentralized cloud nodes. The transition to more robust, state-resistant security protocols was accelerated as the potential for geopolitical fallout became undeniable. Ultimately, the sector moved toward a more cautious and resilient model, prioritizing the continuity of life-saving services over the convenience of total digital integration.