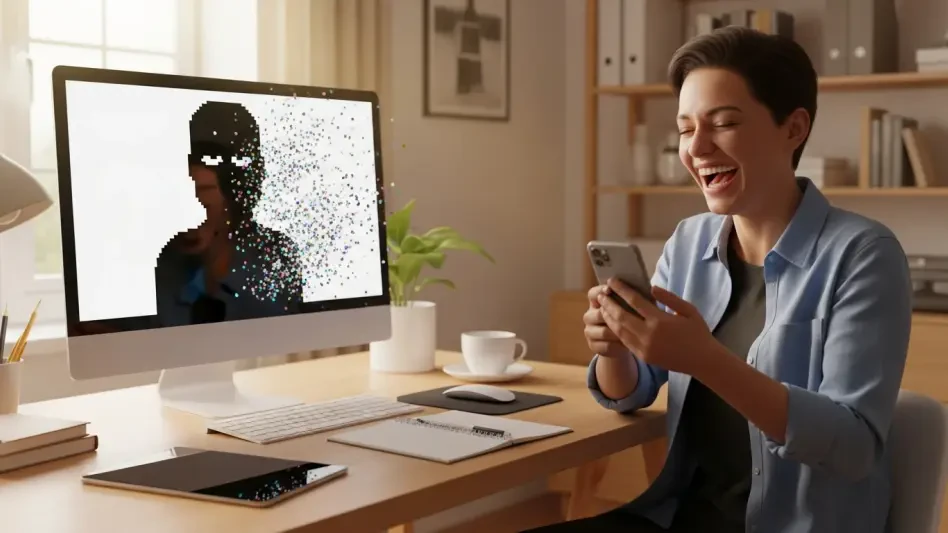
The terrifying realization that a private digital life has been exposed on the dark web is usually enough to send any person into a state of absolute financial panic. A high-level cybersecurity executive claims your IP address is leaked on the dark web and demands $200 for a “protection chip”—but instead of a credit card number, you offer to pay in wheels of artisanal brie. This was the reality for digital security advocate Becky Holmes, who turned a high-stakes extortion attempt into a viral lesson in scam-busting. By refusing to follow the criminal’s script, Holmes demonstrated that the most effective way to disarm a digital predator isn’t always a firewall, but a well-timed joke.
This unconventional approach highlights a growing movement in digital literacy where the victim ceases to be a passive participant in a crime. As online threats become more personalized, the traditional methods of ignoring or blocking messages are being supplemented by active subversion. When humor is introduced into a situation designed to be frightening, the entire power dynamic of the interaction shifts instantly.
The Psychological Mechanics of the Modern Social Engineering Crisis
Online fraud has evolved from poorly spelled emails into sophisticated psychological operations designed to trigger immediate panic. Scammers now leverage pseudo-technical jargon and manufactured urgency to bypass a victim’s logical reasoning, often posing as authority figures or recovery specialists. They rely on a specific emotional environment where the target feels uneducated and vulnerable. By establishing themselves as “experts” who can solve a problem the victim didn’t know they had, criminals create a sense of dependency.
Understanding this shift is critical, as these criminals thrive on the victim’s fear of the unknown. When the terror of a “dark web leak” becomes the primary motivator, traditional security education often fails to keep pace with the emotional manipulation at play. This psychological pressure is intended to move the victim toward a quick, irrational decision before they have time to consult a legitimate professional or think through the absurdity of the claims.
Dismantling the Scammer’s Playbook Through Subversion
Digital predators like the “Sandra Lindsay” persona use terms like “IMEI tracking” and “dark web monitoring” to create a sense of impending doom. These phrases are carefully chosen to sound technical enough to be plausible but vague enough to be terrifying to a non-expert. However, most cybercriminals operate using strict, rigid templates that rely on the victim remaining within a narrow range of responses. When a target deviates from the expected fearful response by introducing nonsensical comments, the fraudulent narrative quickly falls apart.
By introducing absurdity—such as claiming the dark web is simply “searching Google with the lights off”—the victim transforms from a passive target into an active interrogator. This practice, often referred to as “scambaiting,” goes beyond mere avoidance by engaging fraudsters to waste their time and gather intelligence on their evolving tactics. When the scammer is forced to go off-script to address ridiculous claims about artisanal cheese, their professional facade disappears, revealing the amateur nature of the operation.
Expert Insights into the Efficacy of Humor as a Shield
Security advocates and behavioral psychologists note that humor acts as a cognitive “circuit breaker” against the fight-or-flight response that scammers try to induce. By laughing at a threat, the brain regains its ability to process information logically, allowing the individual to spot inconsistencies that were previously hidden by fear. Public reactions to the Holmes incident suggest that demystifying these threats through social media engagement makes the tactics feel less intimidating and more manageable for the general public.
Research into digital literacy highlights that individuals who can identify the absurdity in a scammer’s claims are significantly less likely to fall victim to financial extortion. This cognitive shift is vital because it moves the defense strategy from a technical level to a behavioral one. Instead of relying solely on software to filter out bad actors, the human element becomes a resilient barrier that is much harder for a social engineer to bypass through simple manipulation.
Practical Strategies for Neutralizing Digital Extortion
To effectively counter these threats, individuals should first recognize the red flags of manufactured urgency, especially when a “specialist” uses fear to demand immediate payment or sensitive hardware identifiers like IMEI numbers. If an interaction feels suspicious, testing the script with unconventional or nonsensical responses can quickly reveal if the caller or messenger is following a pre-written fraud template. Legitimate technical support or security firms will never respond with hostility or confusion when asked an unusual question.
It is equally important to verify technical claims independently by using legitimate, third-party resources to check for actual data breaches. Reporting and publicizing these interactions on official channels and social platforms turns a private threat into a public educational tool. This collective approach to security reduced the mystery surrounding digital extortion, ensuring that future attempts were met with skepticism rather than compliance. The shift toward proactive engagement helped establish a new standard where informed resilience was the primary defense against psychological warfare.