The modern battlefield is no longer defined by the reach of a missile or the thickness of an armored hull, as evidenced by the digital persistence displayed during recent high-intensity conflicts. When “Operation Epic Fury” and “Operation Roaring Lion” launched a series of kinetic strikes against Iranian targets in early 2026, many expected a significant degradation of the nation’s offensive capabilities. Instead, observers witnessed a surge in malicious cyber activity that seemed almost entirely uncoupled from the physical destruction occurring on the ground. This phenomenon raises critical questions about how state-sponsored Advanced Persistent Threats (APTs) manage to maintain operational continuity even while their domestic infrastructure is under heavy fire.
Examining Iranian Cyber Readiness and Strategic Response Mechanisms
The core of this research explores the strategic foresight of the Iranian Ministry of Intelligence and Security (MOIS) and the Islamic Revolutionary Guard Corps (IRGC). By analyzing the weeks surrounding the military escalations, researchers identified a sophisticated decoupling of digital assets from national geography. The study specifically investigates how these entities utilized decentralized infrastructure to ensure that a physical strike in Tehran would not result in a digital blackout for their overseas operations.
This resilience suggests a fundamental shift in the doctrine of hybrid warfare, where the digital front operates on a separate plane of existence from the kinetic one. Traditional military deterrence, which relies on the threat of physical consequences, appears increasingly ineffective against an adversary that has successfully offshored its primary operational tools. The ability to project power through code, even while defending against physical incursions, indicates that the Iranian cyber apparatus has matured into a globalized entity rather than a localized military wing.
Background: The Evolution of Hybrid Warfare in the Middle East
The escalation in February 2026 served as a pivotal case study for understanding the integration of cyber operations into broader national defense strategies. Following the mobilization of the IRGC, the international community observed a seamless transition from peacetime espionage to wartime disruption. This shift was not merely a reaction to external pressure but a calculated move to demonstrate that Iranian digital influence extends far beyond its sovereign borders.
Understanding this evolution is critical because it challenges the efficacy of current international security frameworks. If a nation can maintain its offensive reach while its physical command centers are compromised, the logic of “proportionate response” in traditional warfare begins to fail. The Iranian model demonstrates a successful blend of state-sponsored intelligence and decentralized technical assets, creating a blueprint for other nations seeking to mitigate the impact of physical military inferiority through digital dominance.
Research Methodology, Findings, and Implications
Methodology
The investigation utilized advanced data from Augur Security, employing artificial intelligence and behavioral modeling to track shifts in network infrastructure. This approach allowed researchers to look past simple IP addresses and instead focus on the long-term patterns of “bulletproof” hosting and shell company registration. By monitoring three distinct tiers of obfuscation—ranging from domestic Iranian ISPs like Sefroyek Pardaz Engineering to international providers in the West—the analysis created a comprehensive map of the IRGC’s digital footprint.
Furthermore, temporal correlation played a vital role in establishing the proactive nature of these operations. Analysts scrutinized Classless Inter-Domain Routing (CIDR) block activity, looking for spikes in registration and traffic movement that occurred months before the first kinetic engagement. This data provided the necessary evidence to conclude that the cyber offensive was a pre-planned component of the national defense strategy rather than a spontaneous retaliation.
Findings
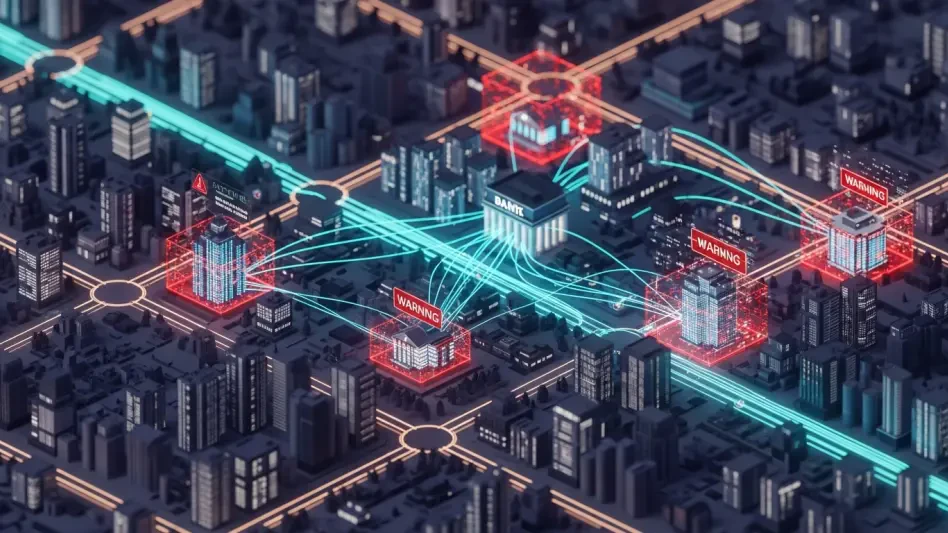
Evidence revealed that Iranian cyber units began systematic infrastructure staging as early as six months prior to the 2026 military strikes. This proactive planning allowed groups like MuddyWater and Charming Kitten to establish a presence in foreign jurisdictions long before tensions reached a breaking point. When the kinetic strikes finally commenced, a centralized “Electronic Operations Room” was activated within 24 hours, successfully coordinating approximately 60 disparate hacktivist groups alongside professional state actors.
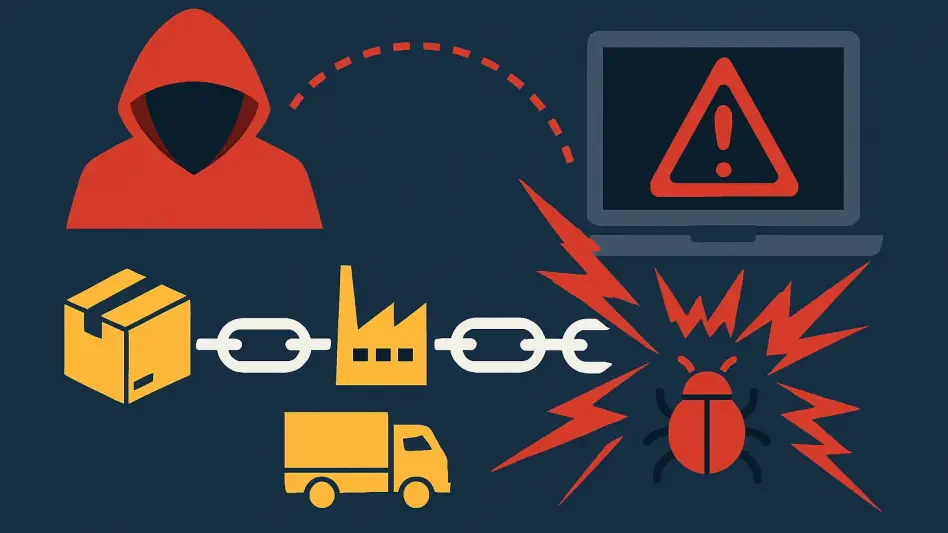
The most striking finding was that physical bombardment failed to significantly degrade these capabilities. Because the IRGC’s digital infrastructure is globally distributed across countries like Moldova, Estonia, and the Netherlands, the units remained operational despite domestic connectivity issues. The study identified that the use of shell companies, such as Cloudblast and UltaHost, provided a layer of legal and geographical insulation that traditional military intelligence found difficult to penetrate in real-time.
Implications
The results of this research indicate that physical force is an insufficient tool for neutralizing modern, decentralized cyber threats. When an adversary’s tools are hosted in the cloud and managed via international shell companies, a cruise missile becomes an obsolete solution for a digital problem. This reality necessitates a shift in defensive posture, moving away from purely military responses and toward the disruption of the financial and legal frameworks that allow state-sponsored actors to hide in plain sight.
Moreover, the successful integration of grassroots hacktivism with elite intelligence units provides a resilient model for hybrid conflict. By masking state actions behind a “citizen” collective, nations can maintain plausible deniability while executing high-impact disruptions. Future defensive strategies must account for this blending of roles, as the line between a patriotic civilian hacker and a professional intelligence officer continues to blur in the digital domain.
Reflection and Future Directions
Reflection
The study highlighted the immense difficulty of attributing and dismantling networks that exploit the complexities of international business law. Navigating the web of dual-registered shell companies proved to be a significant forensic challenge, as these entities often use legitimate commercial services to mask their true intent. The research also underscored that while AI-driven mapping is highly effective, the speed at which threat actors can rotate their infrastructure still outpaces many traditional defensive response times.
The findings suggested that the IRGC has moved beyond simple defensive measures, favoring a strategy of “forward-deployed” digital assets. This ensures that their counter-strike capability remains intact regardless of the status of the Iranian mainland. While the analysis was thorough, it also pointed to a need for deeper investigation into the specific automation tools used by these groups to manage their vast, multi-national network of servers and proxies.
Future Directions
Upcoming research should focus on the role of international hosting regulations and the potential for stricter ICANN enforcement to limit the use of shell companies by state actors. There is a pressing need to determine if international law can be updated to hold hosting providers more accountable for the activities occurring on their networks without stifling legitimate digital commerce. Strengthening these legal barriers could prove more effective than any physical strike in curbing state-sponsored cyber aggression.
Additionally, further exploration into the “Electronic Operations Room” model is essential for understanding how centralized command structures manage decentralized collectives during high-intensity conflicts. Scientists and strategists must determine how to disrupt the communication channels between state leaders and these hacktivist groups. Developing specialized AI models to predict infrastructure rotation before it occurs will be the next logical step in staying ahead of an adversary that has already mastered the art of digital survival.
Summary of Iranian Cyber Resilience and Strategic Shifts
The analysis demonstrated that the Iranian cyber apparatus successfully achieved a high level of resilience by integrating global infrastructure with rapid tactical mobilization. These findings confirmed that the IRGC effectively adapted to kinetic pressure, ensuring that digital operations remained largely unaffected by physical damage sustained at home. This study contributed to the field of security studies by highlighting the urgent necessity of a multi-domain defensive approach that prioritizes the disruption of digital supply chains over traditional territorial strikes. Ultimately, the research showed that in the era of hybrid warfare, territorial sovereignty no longer dictates the boundaries of a nation’s ability to wage war.