The rapid transformation of Iranian cyber operations from localized digital disruptions into a cohesive instrument of global power projection has fundamentally altered the calculus of modern international security. What began as a series of regional skirmishes has matured into a sophisticated doctrine that leverages digital assets to project influence far beyond the borders of the Middle East. This evolution reflects a calculated move by Tehran to utilize asymmetric tools to bypass traditional military limitations, allowing the state to challenge much larger global powers without engaging in direct conventional warfare.
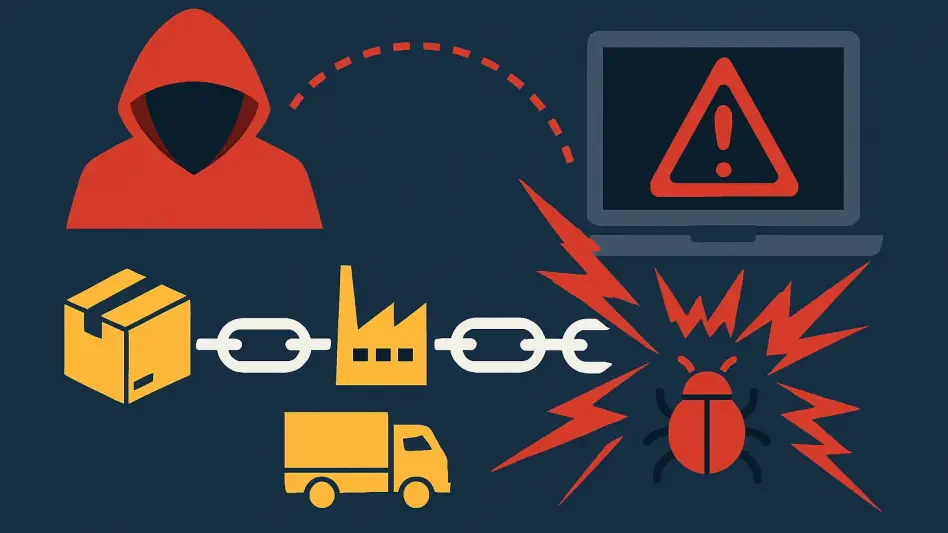
At the heart of this strategy lies a complex ecosystem of state-sponsored entities and decentralized proxy groups that provide the regime with a degree of plausible deniability. These actors operate under a digital doctrine that prioritizes disruption over traditional espionage, effectively serving as the vanguard of a broader geopolitical struggle. By empowering various groups with diverse skill sets, the central government creates a resilient network capable of launching simultaneous strikes across multiple continents, making the identification and containment of these threats a constant challenge for international intelligence agencies.
The strategic focus has increasingly shifted toward critical infrastructure, medical technology, and defense logistics, marking a departure from purely political or economic targets. Recent operations demonstrate a specific interest in sectors that maintain the foundational stability of Western societies, such as water treatment plants and electrical grids. By infiltrating these systems, Iranian actors seek to demonstrate the vulnerability of civilian life, creating a psychological ripple effect that extends well beyond the immediate technical damage.
Perhaps the most defining characteristic of this new era is the pervasive adoption of the wiper philosophy, which emphasizes systemic destruction over financial extortion. Unlike many global criminal syndicates that use ransomware to generate revenue, Iranian-linked groups often deploy malware designed to permanently erase data and paralyze hardware. This focus on operational termination suggests that the primary goal is not profit, but rather the infliction of maximum friction and the erosion of public trust in essential services.
Strategic Shifts and the Rising Data of Digital Conflict
Emerging Tactical Trends and the Pursuit of Total Friction
Current tactical trends reveal a deliberate move toward high-impact, low-sophistication attacks that utilize widespread tools like Distributed Denial-of-Service and high-profile website defacement. These methods, while technically simpler than custom-coded zero-day exploits, allow for rapid deployment and massive visibility, particularly when paired with hack-and-leak operations. By dumping sensitive internal communications into the public domain, these actors create internal chaos within targeted organizations, forcing them to divert significant resources to crisis management and public relations.
Furthermore, there is a growing integration of cyber operations with kinetic military objectives, where digital breaches are used to harvest intelligence for physical targeting. In recent months, attempts to infiltrate closed-circuit surveillance networks and industrial control systems have provided vital data that could theoretically assist in guiding missile systems or identifying high-value physical assets. This convergence signifies that the digital realm is no longer a separate theater of war but an essential component of a unified military strategy designed to achieve physical results through virtual means.
The role of psychological operations has also expanded, with social engineering campaigns becoming a staple of Iranian interference in foreign democratic processes. By creating artificial news cycles and impersonating activists on social media, these agents of influence attempt to deepen existing social divisions and undermine the legitimacy of institutional leadership. This method of digital friction aims to weaken the domestic resolve of adversaries, making it more difficult for them to maintain a coherent foreign policy stance in the face of internal unrest.
Quantifying the Surge in Global Cyber Interference
Since the beginning of 2024, there has been a documented uptick in aggressive digital activity against American and allied industrial sectors, reflecting a heightened state of global friction. Statistical analysis of these incidents shows that the frequency of attempts to penetrate critical supply chains has reached unprecedented levels, with a specific focus on defense contractors and logistics providers. These efforts are not merely exploratory; they represent a concerted attempt to identify “soft spots” in the global distribution network that could be exploited during a wider conflict.
The performance indicators of these chaos agents suggest a high level of success in disrupting global supply chains, even when the intrusions are detected early. The mere presence of a state-sponsored actor within a sensitive network often triggers costly shutdowns and extensive forensic investigations that delay production and delivery. These delays serve as a form of digital attrition, slowly wearing down the economic and operational capacity of adversaries by forcing them to operate in a constant state of defensive high alert.
Projections for the remainder of the year and into 2027 suggest that this digital attrition will only intensify as physical geopolitical tensions remain high. As traditional diplomatic channels struggle to resolve underlying conflicts, the digital battlefield remains an attractive arena for escalation that stops just short of declaring open war. This persistent state of conflict ensures that private sector entities will continue to bear the brunt of geopolitical posturing, requiring a total reassessment of how corporate risk is calculated in a borderless world.
Navigating the Obstacles of Asymmetric Digital Warfare
One of the most significant challenges in this landscape remains the difficulty of accurately attributing attacks to state actors versus independent proxies. Tehran often utilizes a “front” of independent patriotic hackers who appear to act of their own volition, complicating the legal and diplomatic response from the international community. This blurred line between official state policy and rogue activity allows the government to distance itself from the most destructive operations while still reaping the strategic benefits of the chaos they cause.
There is also a widening resource gap between sophisticated state actors and the essential public sectors they often target. Local municipalities, small-scale utilities, and regional healthcare facilities frequently lack the cybersecurity capital necessary to defend against persistent, well-funded threats. This creates a scenario where the weakest link in the national infrastructure becomes a gateway for broader systemic failure, as these smaller entities are often interconnected with larger state and federal networks through shared data portals and supply chains.
Countering wiper malware and permanent data destruction requires a shift in defensive philosophy from prevention to rapid recovery and resilience. Traditional perimeter defenses are often insufficient against attackers who use stolen credentials or social engineering to bypass firewalls. Consequently, organizations must invest in immutable backup solutions and air-gapped data storage to ensure that even a successful destructive attack does not result in total operational failure. Hardening these soft civilian targets is no longer an optional security measure but a mandatory requirement for national stability.
The Regulatory Response and the Push for Cyber Hygiene
In response to these escalating threats, the Department of Homeland Security and various international bodies have accelerated the implementation of rigorous defense standards. The move toward Zero Trust architectures, which assume that every user and device is a potential threat until proven otherwise, has become a cornerstone of recent regulatory mandates. These frameworks require constant authentication and limit the lateral movement of any single user within a network, significantly reducing the potential blast radius of an Iranian-led intrusion.
Immediate patching protocols and the removal of legacy systems have also transitioned from best practices to regulatory necessities. Government-led warnings regarding specific Iranian tactics have prompted a surge in private sector security investments, as companies recognize that compliance is a critical component of their overall defense. By establishing a unified front through mandatory reporting of incidents, the public and private sectors can share threat intelligence in real time, allowing other potential targets to immunize their systems before the same malware reaches their doorstep.
Furthermore, compliance is increasingly viewed as a form of strategic deterrent. When an entire industrial sector adopts standardized security protocols, the cost and effort required for an attacker to achieve a successful breach increase significantly. This collective defense model aims to change the cost-benefit analysis for Iranian cyber commanders, potentially steering them away from hardened sectors and toward less critical targets where the strategic impact is minimized.
Future Projections: The Convergence of Adversarial Networks
The potential for a united front involving technical assistance from other major powers like Russia and China remains a high-risk scenario for the near future. While each nation has its own distinct objectives, the shared goal of undermining Western dominance creates opportunities for the exchange of sophisticated tools and methodologies. If Iranian actors gain access to advanced Russian malware or Chinese-scale infrastructure for launching attacks, the lethality and reach of their operations could experience an exponential increase.
Artificial Intelligence is expected to play a transformative role in scaling Iranian disinformation and social unrest campaigns. By using AI to generate highly convincing deepfake content and automated social media bots, state actors can flood the information environment with conflicting narratives at a speed and volume that human moderators cannot match. This technology allows for a more personalized form of social engineering, where messages can be tailored to specific demographics to maximize their emotional and political impact.
The next phase of conflict will likely transition from simple data theft to the direct manipulation of physical infrastructure through the Internet of Things. As more industrial processes are connected to the web, the risk of a cyberattack causing physical damage or loss of life becomes more acute. Future defense strategies must therefore focus on the physical consequences of digital breaches, developing innovative methods to isolate critical physical controls from the vulnerable public-facing components of a network.
Concluding Perspective on the New Era of Digital Attrition
The transformation of Iran into a global chaos agent signaled a fundamental shift in how modern states pursued geopolitical interests. By prioritizing the destruction of data and the disruption of essential services, Tehran effectively moved the front lines of conflict into the civilian sphere, forcing private organizations to become unwitting participants in a larger state-on-state struggle. The traditional boundaries of geography and military might were rendered less relevant by a digital doctrine that thrived on asymmetry and plausible deniability.
Organizations that successfully navigated this volatile period did so by prioritizing fundamental cyber hygiene over the pursuit of flashy but unproven technological solutions. The focus on immediate patching, multi-factor authentication, and the hardening of internal networks proved to be the most effective defense against the wave of low-sophistication, high-impact attacks that defined the era. Security leaders learned that resilience was not found in a single piece of software, but in a culture of constant vigilance and rapid response.
Looking forward, the long-term outlook for global security remained defined by a borderless and digitally-contested landscape where attrition was the primary mode of engagement. The international community recognized that traditional deterrence models had to be supplemented with a robust system of information sharing and collective defense. As the digital and physical worlds continued to merge, the ability to maintain the integrity of infrastructure became the ultimate measure of a nation’s strength and stability in an age of permanent volatility.