The modern landscape of digital warfare has moved beyond the flashy destruction of core servers toward a subtle, pervasive quietude where the humble office router serves as the primary gateway for international intelligence theft. This shift represents a fundamental transformation in how state-sponsored actors perceive the network perimeter, moving from the fortified core to the neglected edge. As of 2026, the global intelligence community has identified a massive campaign orchestrated by the Russian-backed entity known as APT28, also referred to as Fancy Bear or Forest Blizzard. This group, operating under the direction of the Main Directorate of the General Staff of the Armed Forces, has redefined the methodology of digital surveillance by exploiting the very hardware that connects the world’s most sensitive offices to the public internet.
The Vulnerable Edge: The Rise of Router-Based Espionage in Modern Conflict
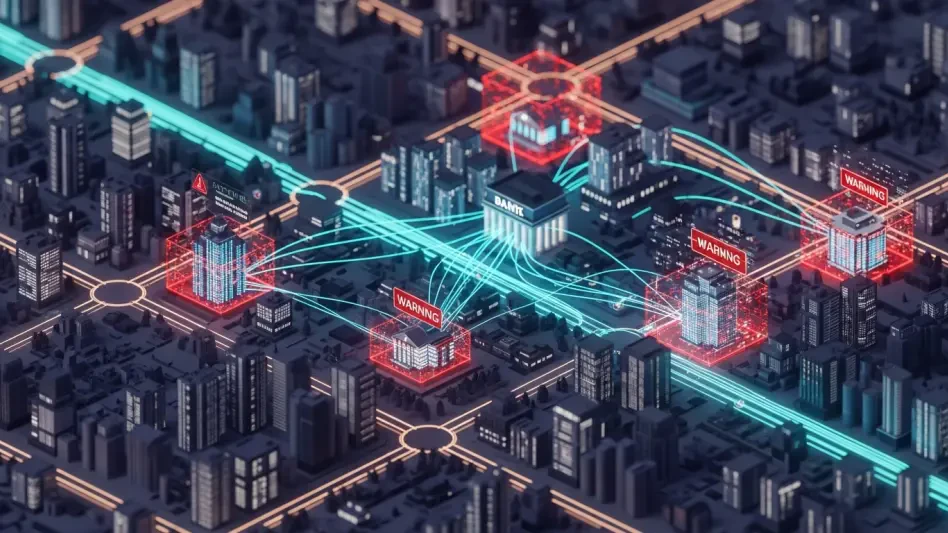
The strategic pivot toward edge-device exploitation signals a new era in state-sponsored intelligence gathering, where the focus has moved away from the complex infiltration of internal servers toward the compromise of perimeter hardware. By targeting the entry and exit points of a network, APT28 effectively gains a vantage point that allows for the monitoring of all outbound communications without ever needing to trigger internal security alarms. This campaign has achieved a global scale that is nearly unprecedented, impacting thousands of government and military entities across more than 120 countries. The use of small office and home office hardware as a primary vector highlights a systemic failure to treat peripheral devices with the same security rigor as centralized data centers.
This GRU-backed operation prioritizes low-effort, high-impact digital surveillance, utilizing known vulnerabilities in consumer-grade and entry-level enterprise hardware. These devices are frequently the soft underbelly of critical infrastructure, often deployed in satellite offices or by remote workers who handle sensitive national security data. Because these units are rarely monitored with the same intensity as primary corporate firewalls, they provide a persistent and stealthy platform for long-term data collection. The sheer volume of compromised devices across diverse geographical regions indicates a coordinated effort to build a global proxy network capable of obscuring the origins of further malicious activities.
Evolution of Tactics: From Malware Binaries to Fileless DNS Hijacking
Shifting Landscapes and the Pivot to Configuration-Based Attacks
The tactical evolution of APT28 reveals a sophisticated understanding of modern detection capabilities, leading the group to move away from identifiable malware tools like Authentic Antics in favor of stealthy configuration changes. In previous years, threat actors relied on custom binaries that could eventually be isolated and analyzed by security researchers. However, the current methodology focuses on altering the fundamental routing instructions of the device itself. This agility is best demonstrated by the group’s ability to modify its attack infrastructure within 24 hours of public disclosure by national security agencies, ensuring that defensive measures are often outdated by the time they are implemented.
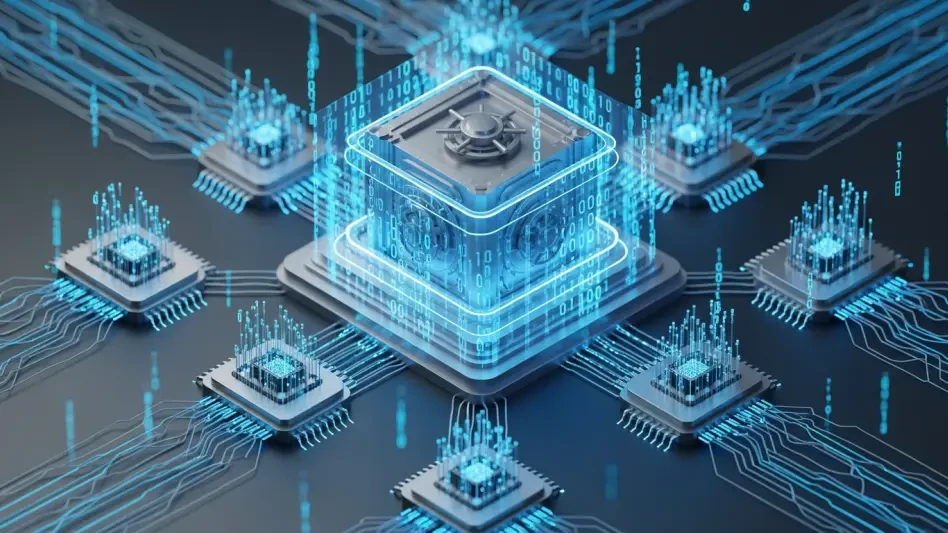
The fileless nature of these attacks represents a significant challenge for traditional security architectures, as there is no malicious code residing on the device to be flagged by endpoint detection or antivirus tools. Instead of installing a virus, the actors simply change the address of the Domain Name System server that the router consults. This redirection happens at the protocol level, meaning the device continues to function exactly as intended while silently sending sensitive traffic to an unauthorized destination. Because the compromise exists only as a modified setting in the router’s administrative interface, it remains invisible to nearly all standard monitoring solutions that look for suspicious processes rather than unauthorized configuration states.
Scaling the Operation: Market Reach and Data Interception Projections
The industrial scale of this campaign is evidenced by the identification of over 18,000 unique IP addresses tied to malicious infrastructure, creating a massive web of intercepted data points. This reach is expected to grow as decentralized government and law enforcement offices continue to rely on unmanaged hardware to support a distributed workforce. The campaign focuses on high-value targets, specifically those utilizing Microsoft Outlook on the Web, where redirect-based credential harvesting has proven exceptionally effective. By intercepting the initial login request at the router level, APT28 can present a near-perfect replica of a login page, capturing session tokens and passwords before the user even reaches the legitimate service.
Projections for the coming period indicate that as organizations move more services to the cloud, the value of the edge device as an interception point will only increase. The move toward cloud-native environments often reduces the visibility of internal IT teams over the transit path of their data, making the router the last line of defense and the first point of failure. The performance of these redirect attacks shows that even users with advanced training can be deceived when the compromise occurs at the architectural level of the network. This systemic risk is compounded by the fact that many affected entities are located in regions with limited cybersecurity infrastructure, allowing the GRU to maintain a persistent presence with minimal resistance.
The Architectural Weakness: Why SOHO Devices Are the Ideal Proxy
SOHO routers are inherently limited by their design, which prioritizes ease of use and low cost over robust security features or automated patching capabilities. Most consumer-grade hardware does not include the sophisticated logging and telemetry found in enterprise-grade switches, meaning that an administrative change can go undetected for the entire lifespan of the device. This lack of transparency makes it nearly impossible for IT teams to perform effective forensic analysis after a suspected breach. Without a standardized way to export logs to a central security information and event management system, the compromised router remains a black box that continues to serve the interests of the attacker.
Furthermore, the requirement for manual firmware updates creates a persistent environment of vulnerability, as few small office managers have the technical expertise or the time to track and apply security patches. This leads to a situation where vulnerable-by-design hardware persists in sensitive environments for years after a critical flaw has been publicly disclosed. The difficulty of managing these devices at scale means that even when a vulnerability is known, the remediation process is so fragmented that the threat actors can continue to find easy targets. The persistence of these devices in the field provides APT28 with a reliable and renewable pool of proxy nodes that are difficult to defend and even harder to monitor.
The DNS Wild West: Accountability and Protocol Standards in Global Networking
The structural issues surrounding the Domain Name System represent a significant regulatory gap in global networking, as the protocol was never designed with modern state-sponsored threats in mind. There is a distinct lack of unified security oversight for how DNS settings are managed on decentralized hardware, creating a wild west environment that APT28 has exploited with great success. While law enforcement interventions like Operation Masquerade have attempted to disrupt these malicious redirections, such efforts are often reactive and localized. The global nature of the internet means that a disruption in one jurisdiction may have little to no effect on the infrastructure hosted in another, allowing the espionage campaign to persist through geographical hopping.
International standards have yet to mandate secure-by-default configurations for telecommunications hardware manufacturers, leaving the door open for continued abuse of administrative interfaces. The absence of a global mandate for encrypted DNS or mandatory two-factor authentication on all routing hardware has allowed the GRU to weaponize the very protocols that make the internet functional. Until there is a systemic shift in how manufacturers and service providers handle the integrity of the routing path, the DNS system will remain a primary target for actors seeking to intercept data without detection. This accountability gap is a major hurdle in securing the global network against persistent threats that operate at the foundational level of the web.
The Future of Edge Security: Innovation, Automation, and Zero Trust
The move toward automated patch management and hardware-level security tokens represents a potential disruptor to the methods currently employed by APT28. Innovations in firmware delivery are beginning to mirror the seamless update models found in modern operating systems, potentially closing the window of vulnerability that attackers currently exploit. There is also a growing push toward Zero Trust architectures, which operate on the principle that the network’s DNS integrity cannot be assumed. By verifying every request through encrypted channels and identity-based access controls, organizations can mitigate the impact of a compromised router even if the traffic is successfully redirected.
The market for secure-by-design routers is projected to expand as government agencies and large enterprises move away from unmanaged consumer-grade hardware for their remote and satellite offices. This shift involves the deployment of managed edge solutions that provide the same level of visibility and control as core data center equipment. As these technologies become more accessible, the “soft underbelly” of critical infrastructure will become harder to penetrate. The integration of automated threat intelligence feeds directly into edge devices will allow for real-time blocking of known malicious IP addresses, significantly reducing the effectiveness of the proxy networks that APT28 relies on for its global espionage efforts.
Strategic Outlook: Hardening the Global Network Against Persistent Threats
The analysis of APT28’s tactical shift toward DNS-based espionage confirmed that the group successfully exploited the systemic weaknesses of unmanaged edge devices to conduct long-term surveillance on a global scale. This campaign highlighted the dangerous intersection of aging hardware and sophisticated state-sponsored intent, where the lack of automated security updates provided a fertile ground for interception. It was observed that traditional defensive perimeters were insufficient against configuration-based attacks, as the compromise occurred at a layer typically ignored by standard endpoint protection. These findings demonstrated that the integrity of the routing path is just as critical as the security of the data itself.
Moving forward, the primary focus for global security must involve an aggressive transition to enterprise-grade edge solutions that support centralized management and automated patching. The reliance on consumer-grade hardware in sensitive government and military contexts was a significant factor in the success of this espionage campaign. Organizations should prioritize the implementation of DNS over HTTPS or DNS over TLS to prevent unauthorized redirection of traffic at the device level. Furthermore, the adoption of strict multi-factor authentication for all administrative interfaces on networking hardware is no longer optional but a fundamental requirement for maintaining national security.
Ultimately, the digital world was forced to acknowledge that the trust inherent in core routing infrastructure was a liability that could be weaponized by persistent threat actors. The systemic changes required to secure the global network will necessitate a move toward a more transparent and accountable hardware ecosystem where security is an integrated feature rather than an afterthought. By treating the edge of the network with the same level of suspicion as the public internet, the global community can begin to close the loopholes that APT28 utilized so effectively. The lessons learned from this period of widespread exploitation served as the foundation for a more resilient and verified digital infrastructure.