The integrity of the modern digital infrastructure depends heavily on a handful of overworked open-source maintainers whose voluntary contributions power the global economy. This concentrated reliance has birthed a sophisticated new era of cyber espionage where the primary weapon is not a brute-force exploit, but the patient cultivation of professional trust. UNC1069, a hacking collective linked to North Korean interests, has refined this psychological warfare into a precise art form, targeting the individuals behind essential ecosystems like Node.js and npm. Unlike the frantic, high-pressure phishing attempts of the past, these adversaries operate with remarkable composure, often spending several weeks or even months embedding themselves within the professional circles of their intended victims. By leveraging fake LinkedIn profiles and curated Slack identities, they masquerade as recruiters or tech journalists to bypass the natural skepticism of senior developers. This method represents a fundamental shift in threat actor behavior, moving away from broad, automated attacks toward highly surgical, human-centric operations that exploit the inherent openness of the open-source community.
The Architecture of Deception: Beyond Simple Phishing
The operational framework of UNC1069 relies on a meticulously constructed facade of legitimacy that begins long before a single line of malicious code is ever deployed. These actors create deep-cover personas that participate in relevant online discussions, share industry insights, and build rapport with the maintainers of high-traffic software repositories like Mocha, dotenv, and Lodash. Once a relationship is established, the attacker invites the target to a seemingly routine professional interaction, such as a job interview or a podcast recording, hosted on fraudulent versions of ubiquitous platforms like Microsoft Teams, Zoom, or Streamyard. This transition from text-based chat to a live video environment is a critical component of the scheme, as it lowers the victim’s guard through a sense of perceived intimacy and professional validation. During these virtual meetings, the attackers engineer a seamless “technical glitch” that prevents the victim from joining the session correctly, thereby setting the stage for the delivery of the payload.
Building on this foundation of fabricated trust, the attacker suggests a quick technical fix to resolve the supposed connection issue, directing the developer to download a specific utility or patch. This file is not a legitimate troubleshooting tool but a sophisticated Remote Access Trojan (RAT) designed to bypass modern security protocols. Once the maintainer executes this file, the software grants the UNC1069 operators full administrative control over the workstation, effectively neutralizing standard defenses. The group has demonstrated the ability to circumvent two-factor authentication (2FA) and other identity verification layers using advanced specialized tools like WAVESHAPER and HYPERCALL. By gaining this level of access, the threat actors can monitor local environment variables, capture keystrokes, and extract sensitive session tokens. The terrifying reality is that once the compromise occurs at the machine level, the security of the developer’s entire portfolio of software projects is essentially forfeited to the intruder.
Strategic Infiltration and the Long-Term Supply Chain Risk
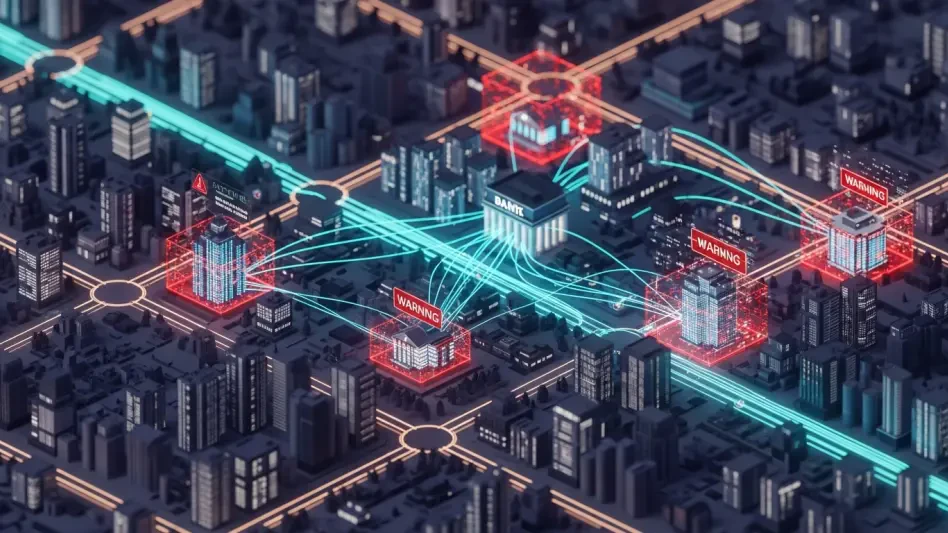
The ultimate objective for UNC1069 is not the theft of individual financial data or personal credentials, but the acquisition of permanent “write access” to major software repositories. By compromising the workstation of a single maintainer, the group can inject malicious code directly into the official update stream of packages that are downloaded millions of times every week. This creates a cascading failure across the global supply chain, as developers worldwide blindly pull these compromised dependencies into their own corporate and government applications. This “poisoning of the well” is far more efficient and damaging than attacking a single enterprise, as it allows the hackers to hide their movements within legitimate software updates that are trusted by security scanners and automated deployment pipelines. The patience displayed by UNC1069 suggests a long-term strategic mission to establish persistent backdoors within the foundational building blocks of the internet’s software stack.
This approach naturally leads to a new normal where the traditional boundaries of cybersecurity must be redrawn to account for human vulnerabilities in the development lifecycle. Security researchers emphasize that the threat is no longer confined to the digital perimeter of a corporation; it now extends to the personal professional interactions of individual contributors. When a maintainer of a package like Lodash is compromised, the downstream impact is nearly impossible to quantify, potentially affecting everything from banking applications to critical infrastructure management systems. The shift in strategy from UNC1069 highlights a sophisticated understanding of the software development ecosystem, where the most valuable asset is the trust shared between a maintainer and their user base. As long as the open-source model relies on the individual integrity of its participants, these highly targeted social engineering campaigns will remain a potent and difficult-to-detect threat to global digital stability.
Actionable Defense: Securing the Human Element
The evolution of UNC1069’s tactics necessitated a move toward more rigorous verification processes for all unsolicited professional engagements within the software development community. Organizations and independent maintainers should adopt a policy of verifying the identity of recruiters or media hosts through multiple independent channels before agreeing to download any software for a meeting. Using dedicated, isolated environments—such as virtual machines or “sandbox” hardware—for virtual calls and interviews can prevent a local machine compromise from spreading to sensitive development environments. Furthermore, implementing hardware-based security keys and strict code-signing requirements can provide a layer of protection that software-based malware struggles to overcome. The focus should shift from merely securing the code to securing the environment in which the code is written, ensuring that even a successful social engineering attempt does not result in unauthorized repository access.
Maintaining a posture of healthy skepticism toward technical troubleshooting requests during virtual meetings is now a mandatory requirement for anyone with administrative access to major repositories. Developers should avoid installing any browser extensions, plugins, or standalone executables suggested by external parties during a call, as these are the primary vectors for modern Remote Access Trojans. Future considerations for the open-source community must include the adoption of multi-signature release processes, where no single maintainer has the power to push an update without the cryptographic approval of several peers. This decentralized trust model significantly raises the bar for attackers like UNC1069, as they would need to successfully compromise multiple targets simultaneously to achieve their goals. By combining technical safeguards with a more cautious approach to digital networking, the software industry can begin to fortify the human links that are currently the weakest points in the global supply chain.