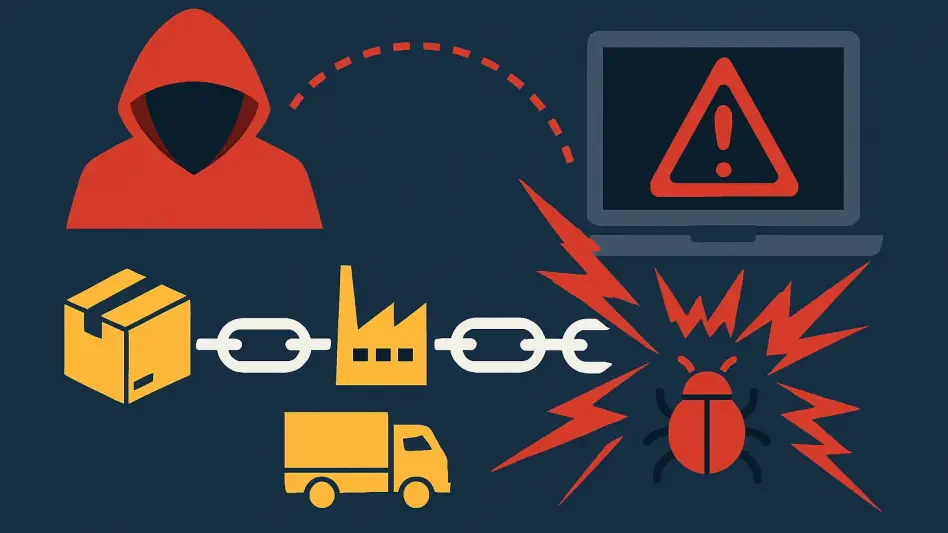
While a typical desktop user might hesitate before opening an attachment from an unknown sender in their corporate email, that same level of scrutiny rarely extends to the familiar green interface of a personal messaging app. A highly sophisticated malware campaign is currently exploiting this exact psychological vulnerability, transforming the casual environment of WhatsApp into a fertile ground for administrative hijacking on Windows systems. By replacing traditional phishing URLs with malicious Visual Basic Script (VBS) files, threat actors are proving that a single misplaced click in a chat bubble is often enough to bypass the multi-layered security defenses that businesses have spent years perfecting.
Beyond the Inbox: When Private Messages Become Public Threats
The danger of this backdoor lies in how it successfully circumvents the standard mental filters used to identify cyber threats. Most employees are well-trained to spot suspicious emails, but the casual nature of instant messaging creates a false sense of security. When a notification appears on a personal device or a desktop client, the user often perceives it as a private interaction rather than a potential entry point for a global malware network. This campaign leverages that comfort to distribute VBS attachments that appear harmless but carry the capability to dismantle a system’s integrity within seconds.
This transition from email to messaging platforms highlights a critical flaw in modern digital habits where users often treat their contact lists as inherently trustworthy. Even if a message appears to come from a known associate whose account has been compromised, the lack of traditional red flags makes the payload far more likely to be executed. This behavioral bypass is the primary engine behind the campaign, allowing the malware to land on professional hardware where it can begin its silent ascent toward full system control.
The Evolution of Social Engineering in the Age of Instant Messaging
The current shift toward messaging-based attacks represents a strategic migration by threat actors into “security vacuums” that exist outside the traditional corporate perimeter. While enterprise email servers are reinforced with aggressive attachment scanning and Data Loss Prevention (DLP) protocols, personal applications often operate in an unmonitored gray area. This lack of visibility ensures that malicious files can reach their destination without being intercepted by the rigorous filters that would have flagged them in an Outlook or Gmail environment.
By targeting the inherent trust users place in their immediate communication circles, attackers are effectively outsourcing the bypass of corporate firewalls to the employees themselves. The campaign is particularly effective because it operates under the radar of traditional security training, which has historically focused almost exclusively on web browsing and email safety. Consequently, the desktop version of WhatsApp has become a neglected flank in the defense of both personal data and corporate networks, allowing scripts to execute in environments that are otherwise heavily guarded.
Living Off the Land: How Attackers Weaponize Standard Windows Utilities
Once the initial script is executed, the technical phase of the attack relies on a methodology known as “living-off-the-land” (LotL). This strategy involves the malware utilizing legitimate, pre-installed Windows tools to carry out its objective, making detection by traditional antivirus software incredibly difficult. To blend in with normal system operations, the script renames common utilities; for example, the file-transfer tool curl.exe is masked as netapi.dll, while the background task manager bitsadmin.exe is disguised as sc.exe.
Furthermore, the attackers ensure that the resulting network traffic remains inconspicuous by hosting secondary payloads on reputable cloud infrastructure like AWS and Backblaze. Because most security monitoring software is configured to trust traffic originating from these major providers, the download of the final backdoor components often goes unnoticed. By repurposing the computer’s own legitimate functions, the malware avoids the need to introduce obviously malicious code, allowing it to maintain a low profile while it prepares the system for full exploitation.
Expert Perspectives on the Collapse of the Traditional Security Perimeter
Industry leaders have observed that the effectiveness of this backdoor is a direct result of the thinning line between personal and professional technology. Yagub Rahimov, CEO of Polygraf AI, pointed out that using personal messaging apps on professional hardware creates a dangerous gap in visibility that most corporate defense tools are not equipped to close. Because these private channels are rarely scrutinized by IT departments, they provide a stealthy pathway for malware to establish a foothold on high-value machines without triggering any immediate alarms.
Once the script gained initial access, it quietly modified the Windows Registry and tamered with User Account Control (UAC) settings to ensure its longevity. Security researchers found that these modifications allowed the backdoor to remain open even after a user rebooted their device, effectively silencing the security alerts that would typically notify a user of a breach. This level of persistence allowed the attackers to transition from a simple script execution to a full administrative takeover, granting them the ability to install unsigned software packages or harvest sensitive local data at their leisure.
Tactical Defense Strategies to Neutralize Messaging-Based Malware
Defending against this specific threat required a fundamental shift toward a “zero-trust” architecture for all digital communications. Vigilance became the primary line of defense, with experts advising that any unexpected attachment—regardless of the sender or the platform—be treated with extreme caution. This was especially true for files utilizing VBS or other executable extensions, which are rarely necessary for legitimate personal communication. On a technical level, organizations began prioritizing behavioral monitoring tools that could identify LotL tactics by detecting when system utilities like bitsadmin.exe were being used in unusual ways.
Ultimately, the most effective long-term solution involved enforcing a strict separation between personal messaging platforms and professional hardware. By isolating private communication channels from the machines that hold sensitive corporate data, individuals and organizations significantly reduced their attack surface. The collapse of the traditional security perimeter meant that the responsibility for safety shifted back to the user’s discretion and the implementation of proactive, behavior-based security measures that did not rely solely on identifying known file signatures.