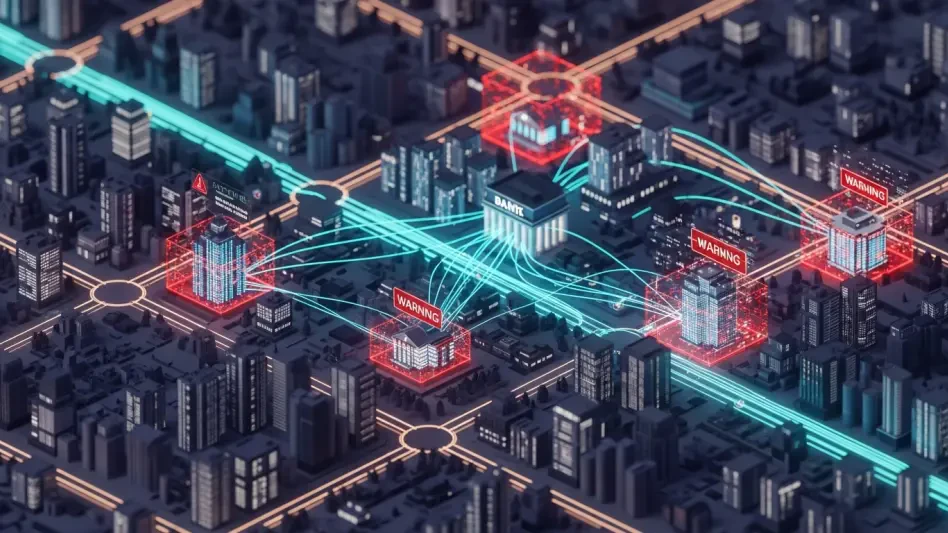
Modern cybersecurity defense perimeters are currently facing an unprecedented challenge as advanced malware samples like DeepLoad begin integrating generative artificial intelligence to produce highly complex layers of obfuscation that traditional scanning tools simply cannot interpret effectively. This specific campaign represents a fundamental shift in how cybercriminals target enterprise environments by blending psychological manipulation with high-speed automated code generation. By moving away from static, predictable payloads, attackers are now capable of deploying software that evolves its appearance for every unique infection attempt, making signature-based detection almost entirely obsolete in the current threat landscape of 2026. Security researchers have noted that this trend signifies a democratization of advanced persistent threat tactics, where even less sophisticated groups can now access tools that mimic the complexity of state-sponsored operations. As these AI-driven threats become more prevalent, understanding the underlying mechanisms of their delivery and persistence is critical for any organization hoping to maintain a secure digital footprint.
The Social Engineering Element: How ClickFix Manipulates Users
The primary infection vector for this malware involves a highly deceptive social engineering technique known as ClickFix, which preys on the innate trust users place in standard operating system prompts. When a user navigates to a compromised or malicious website, they are presented with a realistic overlay that claims a browser error has occurred or a critical update is required to view the content. Instead of a simple download link, the prompt instructs the user to copy a specific string of text and paste it directly into the Windows PowerShell or Windows Terminal utility. This maneuver is particularly insidious because it bypasses the security warnings associated with downloading and opening executable files from the internet. By convincing the user to manually initiate the command, the attacker effectively coerces the victim into becoming an unwitting accomplice in the compromise of their own workstation, effectively bypassing most automated web filters and endpoint protection policies that monitor for suspicious file downloads.
Once the malicious string is executed within the terminal, the malware begins its initial reconnaissance and staging phase by leveraging legitimate administrative tools already present on the system. The command typically initiates a connection to a remote server to fetch a secondary payload, often utilizing the native Windows utility “mshta.exe” to process a remote HTML application. This secondary stage is designed to establish a firm foothold without alerting security operations centers that might be looking for more obvious signs of intrusion, such as the creation of new, unrecognized executable files. The use of PowerShell in this context provides the attacker with broad administrative capabilities, allowing them to modify system configurations and prepare the environment for the arrival of the more complex DeepLoad components. This reliance on living-off-the-land techniques ensures that the initial breach remains as quiet as possible, as the activities are often indistinguishable from legitimate administrative tasks performed by IT staff.
AI-Driven Obfuscation: The Strategy of Digital Noise
A defining characteristic of the DeepLoad malware is its sophisticated use of artificial intelligence to generate massive quantities of “noise” within its source code to overwhelm security software. Traditional static analysis tools function by scanning code for known patterns or suspicious logic; however, DeepLoad circumvents this by embedding its malicious payload within thousands of lines of irrelevant variable assignments and nonsensical operations. Researchers have observed that the volume and variation of this gibberish code suggest the use of large language models to automate the obfuscation process, allowing the malware to change its internal structure every few minutes. This high-velocity mutation ensures that even if one version of the malware is identified and blacklisted, subsequent versions will appear completely different to security scanners. The sheer size of the resulting files can also cause traditional antivirus engines to timeout or skip analysis altogether, as the systems are not optimized to process megabytes of meaningless data for every scanned file.
The integration of artificial intelligence into the malware development cycle allows threat actors to produce highly customized evasion layers at a scale that was previously impossible. This approach transitions the battle from a contest of logic to a contest of computational resources, where the attacker uses AI to create infinite variations while the defender must expend significant processing power to analyze each one. Within the sea of digital noise, the actual malicious instructions are broken apart and scattered, only to be reassembled in memory during the final execution phase. This technique effectively hides the true intent of the software from any tool that examines the file while it is at rest on the disk. By automating the production of these complex wrappers, the creators of DeepLoad have significantly lowered the cost and effort required to maintain an active campaign, ensuring that their tools remain functional even against the most updated and comprehensive security databases available to modern organizations today.
Stealth and Persistence: Exploiting the Windows Environment
DeepLoad maintains its presence within a compromised network by embedding its operations into the Windows lock screen process, a component that is rarely the focus of intensive security monitoring. By hijacking this specific system function, the malware is positioned to intercept sensitive information at the exact moment a user interacts with the operating system. It is capable of harvesting stored credentials from the local security authority subsystem and logging passwords as they are entered by the user during the login process. This placement is strategically advantageous because the lock screen process is considered a core part of the trusted operating system environment, making it an ideal hiding spot for long-term surveillance. The malware can operate silently in the background for weeks or even months, slowly exfiltrating data to external command-and-control servers while avoiding the behavioral triggers that usually accompany more aggressive forms of ransomware or data theft tools.
To ensure that the infection survives system reboots or even standard remediation attempts, the malware utilizes Windows Management Instrumentation event subscriptions. This built-in administrative feature allows the attacker to set up specific triggers—such as a system startup or a user login—that automatically execute the malicious code if it is ever removed from the primary execution path. Because many IT professionals focus their cleanup efforts on traditional areas like the Startup folder or registry run keys, these WMI triggers often go unnoticed, leading to a cycle of reinfection that can frustrate even experienced security teams. This sophisticated persistence mechanism essentially turns the operating system’s own management tools against it, creating a resilient environment where the malware can “resurrect” itself after a perceived deletion. Such deep integration into the Windows framework demonstrates a high level of technical proficiency and a clear focus on maintaining long-term access to valuable corporate assets and sensitive user data.
Strategic Remediation: Building Resilient Security Postures
The emergence of AI-driven malware required a fundamental shift in defensive strategies toward more proactive and behavioral-based monitoring solutions. To counter the specific threats posed by DeepLoad, organizations moved away from relying solely on static signatures and instead implemented comprehensive PowerShell Script Block Logging. This allowed security teams to record and analyze the actual logic of scripts as they executed in real time, regardless of how much obfuscation was applied to the initial code on disk. By monitoring the behavior of the terminal rather than the contents of the file, defenders were able to identify the suspicious patterns of administrative abuse and remote connections that characterize the ClickFix delivery method. Furthermore, the industry adopted a policy of immediate and total credential rotation following any suspected breach, acknowledging that the harvesting capabilities of modern malware made localized password changes insufficient for protecting the broader network infrastructure.
Effective remediation also involved a deeper audit of the internal operating system components that are often overlooked during standard security scans. Specialists recommended that incident response teams perform regular audits of WMI event subscriptions and lock screen process integrity to detect the hidden persistence mechanisms utilized by sophisticated actors. These advanced investigative steps were necessary to ensure that a threat was completely eradicated and could not redeploy itself through automated system triggers. Looking ahead, the focus was placed on zero-trust architectures where terminal access was strictly limited and social engineering training was updated to include the specific risks of copy-pasted commands. This multifaceted approach provided the only reliable way to combat a threat that blended human psychological triggers with high-speed, automated development cycles. By focusing on the underlying behaviors and system-level changes, organizations successfully mitigated the impact of these evolving AI-driven campaigns.