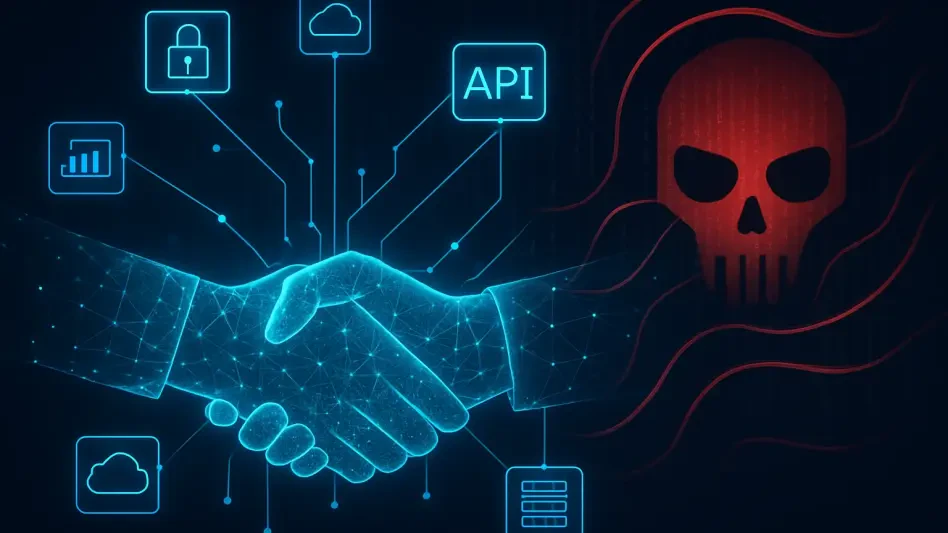
The modern hiring landscape has transformed into a digital battlefield where the next talented software engineer on your Zoom call might actually be a state-sponsored operative working from a secure facility in Pyongyang. As organizations embrace the flexibility of distributed work, they simultaneously open doors to highly sophisticated “insider threats” that bypass traditional perimeter defenses. These individuals do not just hack into systems; they interview for jobs, sign employment contracts, and receive corporate laptops, all while funneling their high-value salaries toward illicit national programs.
This exploration delves into the mechanics of this growing security crisis, examining how foreign intelligence services exploit remote recruitment vulnerabilities. By analyzing the tactical shifts in cyber warfare and the specific methods used to masquerade as domestic workers, readers will gain a comprehensive understanding of the risks associated with global talent acquisition. The objective is to provide a detailed roadmap of these deceptive practices and the red flags that modern security teams must identify to protect their corporate infrastructure.
Key Questions: Understanding the Infiltration Process
What Tactics Do Operatives Use to Bypass Identity Verification?
The success of these infiltrations relies heavily on the ability of an operative to project a legitimate, domestic persona that satisfies the requirements of human resources departments. These actors often utilize stolen or forged identities, complete with realistic resumes and professional social media profiles that mirror the expectations of Western recruiters. By leveraging front organizations like the Willow Tree Economic Technology Exchange Centre, they provide a veneer of institutional credibility that can easily deceive even seasoned hiring managers who are focused on filling technical roles quickly.
Once the initial screening is passed, the operative must manage the technical hurdle of appearing as though they are working from a local residence. This is often achieved through the use of specialized software like Astrill VPN, which allows them to tunnel their internet traffic through exit nodes located in the United States. While they may physically reside in Asia, their digital footprint suggests they are logging in from a suburban neighborhood in Missouri or California. This geographic deception is the cornerstone of their strategy, allowing them to blend into the company’s daily operations without raising immediate suspicion.
How Does the Missouri Mistake Reveal Hidden Security Risks?
Despite the meticulous planning involved in these schemes, the human and technical elements occasionally fall out of sync, leading to critical errors that security teams can exploit. A notable example occurred when an operative’s behavioral patterns diverged from their reported location, triggered by a login attempt from an unmanaged device. This discrepancy, often referred to as the “Missouri Mistake,” happens when an operative fails to maintain the VPN tunnel or connects through a secondary device that lacks the necessary masking protocols. Such anomalies generate high-severity alerts in behavioral analytics platforms, highlighting a disconnect between the user’s supposed domestic identity and their actual physical location.
Furthermore, these incidents illustrate that traditional password-based security is insufficient against an adversary who has legitimate credentials. When an employee is granted access to sensitive Salesforce data or internal repositories, the threat is no longer external; it is baked into the organization’s workflow. Security monitoring must therefore look beyond simple access control and instead focus on consistency in device management and geolocation. When a worker who is supposed to be in one city suddenly appears in another via an unauthorized VPN, it serves as a definitive signal that the “employee” may not be who they claim to be.
What Is the Ultimate Objective of These Corporate Infiltrators?
While many cyberattacks are designed for immediate destruction or data theft, the primary goal of these North Korean operatives is often long-term revenue generation for the state. Many of these individuals are elite graduates who possess genuine technical skills, allowing them to command annual salaries exceeding $300,000. This income is systematically diverted to fund national weapons programs, making every paycheck a direct contribution to geopolitical instability. The dual-purpose nature of their mission means they may perform their job duties competently for months or years while waiting for an opportunity to engage in deeper corporate espionage.
The industrial scale of this operation suggests that the “hacker” has evolved into a full-time corporate professional. They are not merely looking for a quick payout but are integrated into a broader economic strategy managed by the government. This shift complicates the security landscape, as it requires companies to vet their staff not just for technical competence, but for the geopolitical ties and financial destinations of their earnings. The risk of data exfiltration remains a constant shadow, but the immediate threat is the silent exploitation of the global labor market to bypass international sanctions.
Summary: Lessons from the Digital Front Lines
The investigation into these infiltration methods demonstrated that the boundary between a legitimate remote worker and a state-sponsored actor has become dangerously thin. Security experts emphasized that relying on standard recruitment filters is no longer enough to protect sensitive environments from dedicated adversaries. It became clear that proactive threat intelligence and robust behavioral monitoring were the only effective means of catching discrepancies before significant damage occurred. The case highlighted how the intersection of sophisticated VPN usage and identity fraud created a unique challenge for modern corporations.
Successful defense strategies focused on the continuous verification of user behavior rather than just the initial hiring check. Organizations learned that neutralizing such threats required a combination of automated alerts and human oversight to investigate geographical anomalies. By identifying the specific tools and organizations associated with these operatives, companies were able to close the gaps that allowed foreign actors to masquerade as domestic employees. This collective vigilance proved essential in safeguarding both corporate assets and national security interests against industrial-scale fraud.
Final Thoughts: Securing the Future of Remote Work
As organizations continue to expand their remote workforce, the burden of proof regarding identity must shift from a one-time event to an ongoing process of verification. Companies should consider implementing zero-trust architectures that scrutinize every login and device, regardless of the user’s perceived seniority or tenure. Hardening the recruitment process with live, multi-factor identity checks and restricting the use of unmanaged VPNs are no longer optional steps but fundamental requirements for digital survival.
In a world where the person behind the screen could be an agent of a foreign state, staying informed about the latest tactics in social engineering and technical deception is vital. Business leaders and security professionals must work in tandem to foster a culture of skepticism that prioritizes data integrity over hiring speed. By remaining vigilant and adopting advanced behavioral analytics, firms can ensure that their remote teams remain a source of innovation rather than a gateway for state-sponsored infiltration.