The sophisticated nature of modern state-sponsored cyber warfare often relies on the exploitation of mundane hardware that users frequently overlook until a catastrophic breach occurs. In a significant victory for international cybersecurity, a multi-agency coalition led by the United States Department of Justice and the FBI successfully dismantled a pervasive botnet orchestrated by the Russian Main Intelligence Directorate, better known as the GRU. This operation, codenamed Operation Masquerade, targeted a sprawling network of compromised devices that had been weaponized to facilitate high-stakes espionage against government, military, and critical infrastructure sectors. By leveraging vulnerabilities in consumer-grade and small-business routers, the threat group identified as Forest Blizzard managed to infiltrate the digital lives of thousands across the globe, creating a massive pipeline for stolen credentials and sensitive data that remained largely undetected for an extended period of time.
Anatomy of a Global Cyber Espionage Campaign
The Mechanics of Infection: Vulnerable Edge Hardware
The primary vector for this massive infiltration involved the systematic exploitation of over 18,000 devices, primarily focusing on TP-Link and MicroTik routers found in homes and small offices. These devices often run on outdated firmware or possess known security flaws that provide a convenient entry point for sophisticated actors like the GRU’s Unit 26165. Once these routers were compromised, they formed a silent, globally distributed botnet spanning at least 120 countries, effectively turning standard networking hardware into a distributed platform for state-sponsored surveillance. The scale of this campaign demonstrates how state actors have moved away from targeting well-defended corporate servers as their primary entry point, choosing instead to exploit the softer perimeter of the network edge. By controlling these gateways, the attackers were able to monitor traffic and pivot into more sensitive internal networks without triggering traditional security alarms that typically monitor centralized cloud environments or mainframes.
While the initial infection phase appeared to be somewhat opportunistic, the campaign quickly transitioned into a highly refined effort focused on specific high-value intelligence targets. The FBI confirmed that compromised hardware in more than 23 U.S. states was being used as a staging ground for these advanced persistent threats, allowing the GRU to mask its movements behind legitimate domestic IP addresses. This strategy made the malicious traffic nearly indistinguishable from regular internet activity, providing the perfect cover for deep-seated espionage. The list of victims eventually grew to include over 200 distinct organizations, ranging from critical infrastructure providers in North Africa and Central America to military entities in Southeast Asia and various European governmental bodies. This shift from wide-scale infection to targeted extraction highlights a dangerous evolution in how botnets are utilized, moving beyond simple denial-of-service attacks to become essential tools for long-term geopolitical maneuvering and the systematic theft of strategic international data assets.
Technical Exploitation: Hijacking the Domain Name System
The technical sophistication of the operation was matched by the GRU’s use of adversary-in-the-middle tactics to manipulate core internet protocols. By gaining control over the Domain Name System settings on infected routers, the attackers were able to redirect unsuspecting users to malicious domains that were designed to look identical to legitimate web services. One of the most effective methods employed was the creation of fraudulent portals mimicking Microsoft Outlook Web Access, which lured users into entering their login credentials on a site controlled by the Russian intelligence service. This redirection occurred at the router level, meaning that even if the individual’s computer was secure, the network path itself was compromised. This allowed the actors to bypass many standard security measures that focus on device-level protection rather than network-level integrity. The subtle nature of these redirects ensured that most victims had no reason to suspect that their communications were being intercepted by a foreign intelligence agency.
Beyond simple credential harvesting, this method allowed the Forest Blizzard group to capture sensitive OAuth tokens, which are frequently used to maintain access to cloud-hosted environments without requiring repeated logins. By stealing these tokens, the attackers could maintain a persistent presence within an organization’s cloud infrastructure, accessing emails, documents, and private communications at will. What made this approach particularly insidious was that it did not require a direct breach of Microsoft’s internal infrastructure or the servers of any other cloud service provider. Instead, it exploited the trust between the end user and the service by intercepting the authentication process in transit. This allowed the GRU to siphon off vast amounts of sensitive government and military data while remaining invisible to the security teams overseeing the targeted cloud platforms. The result was a massive data-bleeding event that compromised the foundations of international diplomatic and utility sectors, illustrating the critical need for more robust DNS security and multi-factor authentication protocols.
Strategic Response and Remediation Efforts
Public-Private Collaboration: Dismantling the Infrastructure
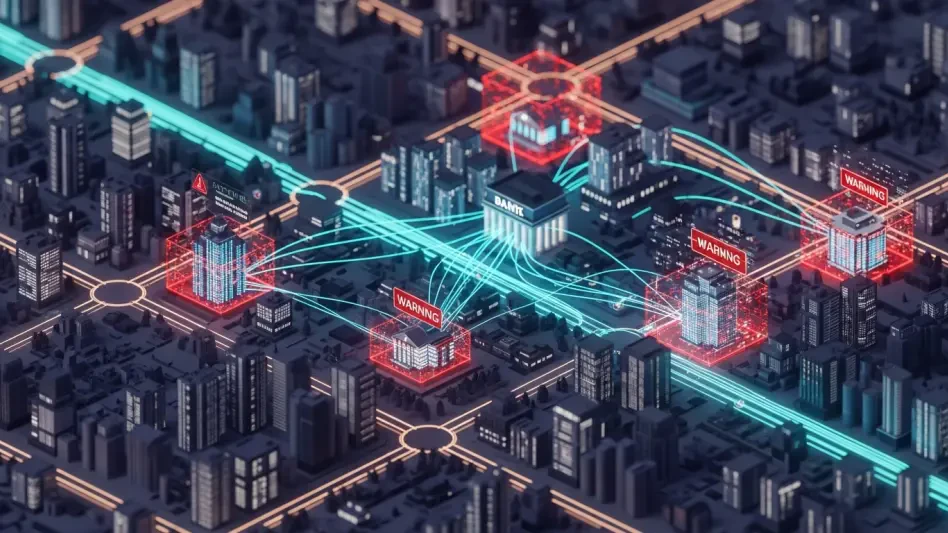
Neutralizing a threat of this magnitude required an unprecedented level of cooperation between government agencies and private sector technology leaders. While the FBI and Department of Justice provided the legal framework and investigative muscle, partners like Microsoft Threat Intelligence and Lumen’s Black Lotus Labs contributed the technical telemetry necessary to map the botnet’s global footprint. This collaborative ecosystem allowed investigators to trace the command-and-control infrastructure back to its origins, identifying the specific patterns used by the GRU to manage their thousands of infected nodes. By synthesizing vast amounts of data from private network traffic and federal intelligence sources, the coalition was able to pinpoint the exact vulnerabilities being exploited and the specific organizations currently under fire. This proactive approach marked a significant shift in federal strategy, moving away from passive warnings toward a more integrated, active defense model that prioritizes the rapid sharing of actionable intelligence across the entire cybersecurity landscape.
The insights gained from private sector researchers were instrumental in understanding the geographic distribution of the threat, which spanned nearly every corner of the modern digital world. Experts at Black Lotus Labs noted that the botnet was particularly dense in regions undergoing significant geopolitical shifts, suggesting that the GRU was using the network to gain an information advantage in ongoing international conflicts. Within the United States, the weaponization of domestic routers posed a unique challenge, as these devices are considered private property yet were being used to attack national interests. The tracking of these 18,000 devices revealed a sophisticated hierarchy where certain routers served as hubs for broader data collection while others acted as simple proxies to confuse attribution. Without the combined resources of both the public and private sectors, identifying these patterns would have been nearly impossible, as no single entity possessed a complete view of the sprawling malicious architecture that Forest Blizzard had meticulously built over several years of operations.
Judicial Intervention: The Process of Active Remediation
Once the scope of the problem was fully understood, federal authorities sought and obtained unique court orders that authorized the FBI to take direct action against the infected hardware. This judicial intervention was a critical component of the operation, as it allowed the government to go beyond mere notification and actually remediate the threat on private devices. FBI technicians sent specialized commands to the compromised routers within the United States to reset their Domain Name System settings and clear the malicious configurations left by the GRU. This process effectively severed the connection between the botnet nodes and their controllers, hardening the devices against future exploitation by the same threat group. This active remediation strategy was necessary because many of the affected routers belonged to individual consumers who likely lacked the technical expertise to recognize the infection or correctly reconfigure their hardware. By taking this bold step, the government was able to halt the data-bleeding event at its source and provide a protective layer for the national network.
In the aftermath of the operation, the collaborative efforts proved successful as data indicated a sharp and permanent decline in communications with the known malicious infrastructure. Organizations were encouraged to adopt more stringent edge-device management policies, including the mandatory use of secure, encrypted DNS protocols like DNS over HTTPS to prevent similar redirection tactics from being effective in the future. Furthermore, the transition toward zero-trust architecture became a necessary evolution for both government and private entities, ensuring that network location was no longer used as a proxy for trust. Regular firmware updates and the decommissioning of legacy hardware that could no longer receive security patches were essential steps for any organization looking to avoid becoming a node in a future state-sponsored botnet. The success of Operation Masquerade demonstrated that while state actors continued to seek out the weakest links in global connectivity, a unified and technically aggressive response could effectively dismantle even the most expansive espionage networks.