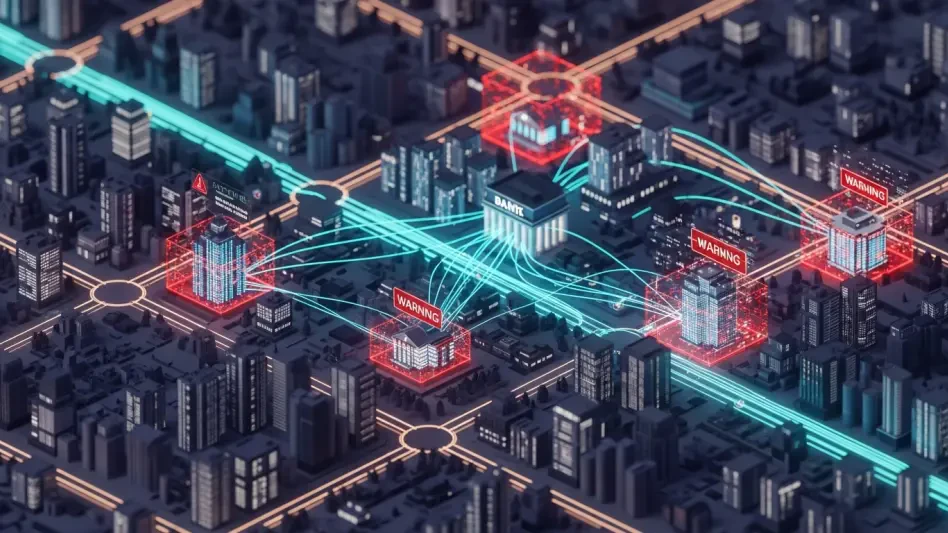
Digital security teams currently face a paradoxical crisis where the very instruments designed to maintain and repair systems are being repurposed as weapons for large-scale data breaches. This phenomenon, increasingly characterized as the “dual-use dilemma,” represents a sophisticated shift in how ransomware operators like LockBit and MedusaLocker approach high-value targets. By leveraging digitally signed IT utilities that are inherently trusted by operating systems, attackers effectively bypass traditional signature-based antivirus protections that would otherwise flag custom-built malware. These tools, which range from system troubleshooting applications to specialized kernel-level utilities, provide the perfect cover for malicious actors to operate under the radar while gaining elevated permissions. As the industry moves through 2026, the reliance on these legitimate binaries has fundamentally changed the risk landscape, forcing administrators to reconsider the safety of their own troubleshooting toolkits.
The Mechanics of Legitimate Software Exploitation
Leveraging Administrative Trust for Kernel Access
The core of this strategy lies in the exploitation of trust established through digital certificates and legitimate software signatures that modern operating systems use to verify program safety. Ransomware groups have begun integrating tools like IOBit Unlocker or Process Hacker into their workflows because these programs possess legitimate administrative capabilities that can be used to terminate critical security services. Unlike traditional malware, which often triggers alerts during installation or execution, these utilities are frequently whitelisted by default within enterprise environments to allow IT staff to perform necessary maintenance. Consequently, when an attacker executes such a program, the system views the action as a routine administrative task rather than a hostile intrusion. This inherent trust allows threat actors to gain kernel-level permissions, enabling them to manipulate deep system processes that are typically protected from external interference, thereby creating a bridge between initial access and full environmental control.
Building on this administrative access, attackers utilize these tools to perform “process killing,” which involves systematically disabling security monitoring software and endpoint detection systems. This stage is critical because it ensures that subsequent malicious actions, such as data exfiltration or encryption, proceed without being logged or blocked by defensive layers. By repurposing legitimate software to shut down security processes, hackers minimize the footprint of their activity, making it nearly impossible for traditional detection mechanisms to distinguish between a routine system update and a coordinated cyberattack. The effectiveness of this approach is amplified by the fact that many of these utilities are portable and do not require a formal installation process, allowing them to be deployed and executed directly from memory or temporary folders. This method effectively strips the target system of its defenses before the actual ransomware payload is even introduced, turning the environment into a vulnerable playground.
Navigating the Multi-Stage Kill Chain
A structured kill chain defines the success of modern intrusions, typically beginning with a breach achieved through sophisticated phishing campaigns or the purchase of stolen credentials from initial access brokers. Once a foothold is established within the network, the transition from simple access to full-scale dominance occurs through a series of calculated steps involving the same trusted IT utilities. During the secondary stage of evasion, attackers deploy specialized tools such as Mimikatz to harvest administrative passwords and session tokens directly from the system memory. This allows for lateral movement across the network without the need to exploit additional vulnerabilities, as the attackers are essentially using the stolen identities of legitimate users. The integration of these tools into a cohesive attack sequence demonstrates a high level of operational maturity among ransomware syndicates, who have moved away from chaotic infection methods in favor of a surgical approach that mirrors the tactics of professional penetration testers.
Following the harvesting of credentials, the focus shifts toward the erasure of forensic evidence to ensure long-term persistence or to complicate post-incident investigations. Tools that were originally designed to manage system logs or optimize storage are frequently utilized to delete event records and clear shadow copies that might contain backups of critical data. By wiping these logs, attackers remove the breadcrumbs that forensic teams rely on to reconstruct the timeline of the breach or identify the specific entry point. This comprehensive approach to evasion not only facilitates the immediate goal of data encryption but also leaves the victim organization in a state of confusion regarding the extent of the damage and the identity of the perpetrators. The ability to manipulate the very systems meant to record activity represents a significant escalation in the ongoing arms race between cybercriminals and defense specialists, highlighting a reality where even the most meticulous logging strategies can be undermined by the misuse of standard administrative utilities.
Strategic Shifts in Ransomware Operations
The Professionalization of Ransomware-as-a-Service
The rise of the Ransomware-as-a-Service model has significantly contributed to the standardization of these dual-use tactics across the global threat landscape. Large-scale operations such as BlackCat and LockBit 3.0 now provide their affiliates with pre-packaged toolkits that include these legitimate IT utilities as part of their standard infection routine. This professionalization means that even less experienced hackers can execute complex, multi-stage attacks that were previously the exclusive domain of state-sponsored actors or elite cybercriminal groups. By providing a structured framework for the misuse of administrative tools, RaaS operators ensure a higher rate of success for their affiliates, which in turn fuels the economic engine of the ransomware industry. This shift toward a more corporate-like structure within the cybercriminal underworld has led to a proliferation of highly effective attacks that prioritize stealth and reliability over raw speed, allowing groups to demand larger ransoms from organizations.
Furthermore, the commoditization of these attack methods has led to a convergence of tactics used by various threat actors, making attribution increasingly difficult for security researchers. When multiple groups utilize the same set of legitimate utilities and follow similar kill chains, distinguishing between a specific ransomware gang and a different motivated adversary becomes a significant challenge. This lack of a unique “digital fingerprint” is a deliberate choice by attackers who recognize that using standard tools provides a degree of plausible deniability and helps them blend into the noise of daily network administration. As these groups continue to share resources and refine their methodologies, the boundary between legitimate IT operations and malicious activity becomes increasingly blurred. This environment necessitates a fundamental shift in defensive strategies, moving away from a reliance on recognizing known malware signatures and toward a more behavioral approach that monitors how administrative tools are being utilized across the enterprise infrastructure.
Anticipating the Integration of Artificial Intelligence
Looking ahead into the current progress of digital threats from 2026 to 2028, the integration of artificial intelligence into these attack frameworks is set to revolutionize the efficiency of dual-use tool exploitation. Experts anticipate a shift toward automated systems that can dynamically analyze a target’s security configuration and automatically select the most effective legitimate utilities to dismantle those specific defenses. Rather than relying on static scripts, AI-assisted malware will be capable of making real-time decisions on which processes to kill or which logs to erase based on the immediate feedback from the host environment. This level of automation will allow attackers to scale their operations significantly, conducting hundreds of simultaneous intrusions with minimal human intervention. The speed and precision of AI-driven tool selection will likely outpace the reaction time of human defenders, creating a scenario where security teams must rely on their own AI-powered defensive measures to stand a chance of neutralizing these threats.
This evolution underscores a critical vulnerability in modern IT infrastructure where the complexity of managing diverse systems requires powerful administrative tools that can also be easily subverted. As AI models become more adept at identifying and exploiting these administrative pathways, the dual-use dilemma will only intensify, making the management of software permissions a primary battlefield in cybersecurity. The potential for AI to automate the discovery of new ways to repurpose legitimate software means that the list of “trusted” applications may constantly shrink, requiring a more dynamic and restrictive approach to software execution policies. Organizations must prepare for a future where the distinction between a helpful utility and a destructive weapon is determined entirely by the context of its use and the intent of the user. Consequently, the focus of digital defense must evolve from simply blocking bad software to understanding the nuanced behavior of authorized programs, ensuring any deviation is met with an immediate response.
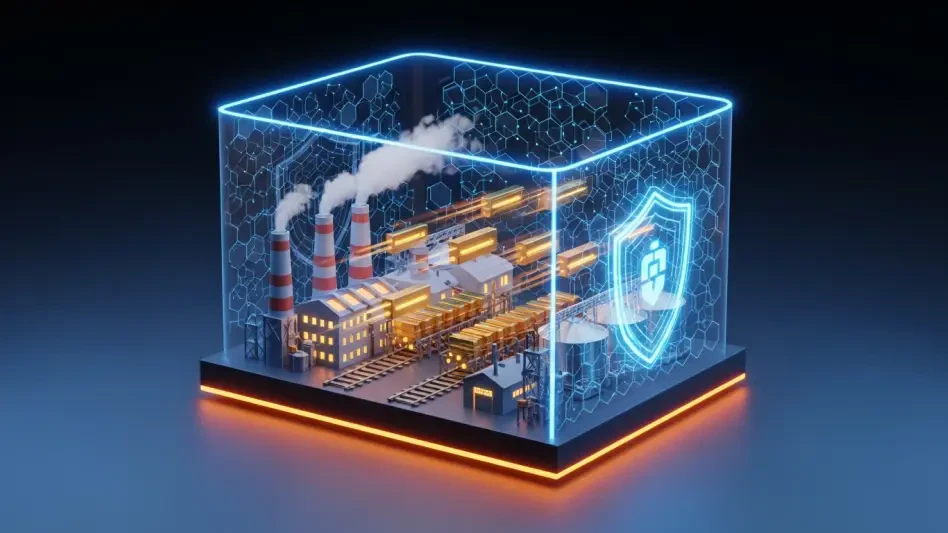
Implementing Proactive Behavioral Safeguards
Organizations that successfully mitigated these sophisticated risks prioritized the implementation of robust behavioral analytics and strict application control policies. They recognized that relying solely on digital signatures was no longer a sufficient defense against modern ransomware groups. Instead, defensive strategies shifted toward monitoring the execution context of administrative tools, ensuring that utilities like Process Hacker or IOBit Unlocker were only accessible to verified users under specific conditions. Security leaders also adopted Zero Trust architectures that restricted the movement of even authorized software across different network segments, thereby limiting the potential blast radius of a compromised utility. By integrating advanced endpoint detection systems with real-time AI monitoring, these organizations were able to identify the subtle transition from legitimate maintenance to malicious exploitation. These proactive measures transformed the defensive posture from a reactive hunt for malware into a comprehensive oversight of all system activities.