The Invisible Threat to Digital Healthcare
The rapid migration of sensitive medical consultations to the digital sphere has fundamentally shifted the security paradigm from defending physical perimeters to safeguarding the psychological boundaries of every staff member. While technical exploits often dominate headlines, the most pervasive risk to telehealth today is social engineering, which leverages human emotion to circumvent sophisticated encryption. As platforms like Hims & Hers expand their reach to millions of users, the “human element” emerges as a critical vulnerability. This analysis examines how these psychological tactics target the support structures of modern medicine, putting patient metadata at risk and challenging the industry to rethink its defensive posture.
The Evolution of Telehealth and Cybersecurity Challenges
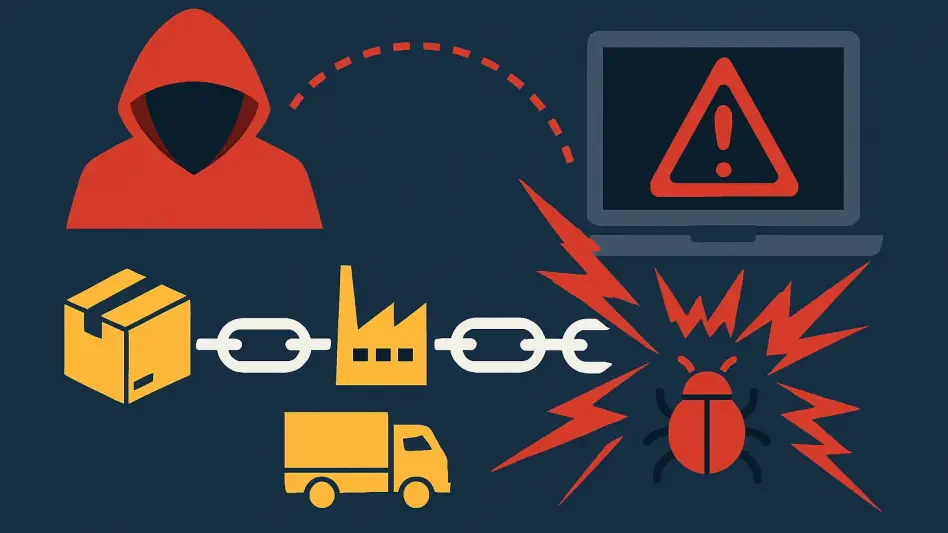
Telehealth has transformed from a niche convenience into a cornerstone of the global medical economy, managing massive volumes of sensitive data through interconnected cloud ecosystems. Historically, health-tech firms prioritized hardening their primary medical databases against direct intrusion, yet the current landscape involves a fragmented array of third-party service providers. This expansion has created a lucrative target for attackers who recognize that while core health records are heavily guarded, the peripheral systems used for customer interaction are often more accessible. The result is a shift in criminal strategy toward exploiting the interconnected nature of modern digital health.
The Human Element: How Social Engineering Bypasses Technical Shields
Manipulating the Help Desk: The Anatomy of a Breach
Social engineering frequently succeeds by exploiting the professional mandate of customer service teams to be helpful and responsive to user needs. In recent incidents, such as the targeting of Hims & Hers in February, threat actors utilized deceptive communications to trick employees into granting access to administrative support environments. These breaches often bypass multi-factor authentication not through code, but through the manipulation of internal authorization procedures. Once inside, attackers gain access to support tickets that serve as repositories for names and contact details, which are then used to fuel secondary fraud.
The Vulnerability of Third-Party Platforms
While a telehealth provider might secure its core electronic medical records, the peripheral customer service platforms frequently represent a significant secondary vector for data exposure. These external environments are essential for managing subscriber inquiries but often lack the same level of isolation as primary medical systems. When these entry points are compromised, the exposure of treatment-related inquiries constitutes a severe breach of trust, even if doctor-patient chat logs remain encrypted. Analysis suggests that attackers are increasingly prioritizing these “soft” third-party targets over traditional, more fortified databases.
Navigating the Psychological Tactics of Modern Phishing
Modern phishing has evolved far beyond generic spam, maturing into highly researched spear phishing and voice-based “vishing” campaigns that target specific organizational roles. Attackers often monitor company expansions, such as new weight-loss medication rollouts, to craft believable narratives that resonate with unsuspecting staff. There is a common misconception that only poorly trained individuals fall for these traps; however, even seasoned professionals can be overwhelmed by high-pressure tactics. This complexity ensures that social engineering remains a persistent threat that software updates alone cannot eliminate.
The Future of Defensive Strategies in Health-Tech
Moving forward, the telehealth sector is expected to move toward “Zero Trust” architectures that restrict the access of any single employee to the absolute minimum necessary. Organizations are likely to integrate AI-driven behavioral analytics to monitor customer service interactions and flag unusual data access patterns in real-time. Additionally, regulatory bodies are increasing the pressure for transparent and rapid disclosures of such incidents. As firms diversify their offerings, the implementation of biometric verification for support staff and stricter auditing of third-party vendors will become standard operational requirements.
Strengthening Your Personal and Organizational Privacy
Combatting these sophisticated psychological attacks requires a dual commitment from both health providers and the consumers who use their services. Companies must implement continuous security stress tests and ensure that every external partner adheres to the same stringent security benchmarks as internal teams. On the individual level, patients should maintain a high degree of skepticism regarding unsolicited communications and use unique, complex passwords for every platform. Awareness that even minor metadata exposure can lead to targeted fraud is the first step in maintaining long-term digital safety.
Securing the Future of Digital Medicine
The resilience of the telehealth industry depended on its ability to address the psychological vulnerabilities that digital infrastructure could not fix on its own. It was determined that the exposure of support tickets and metadata at Hims & Hers represented a significant lesson in how secondary data points remained high-value targets. This era of digital medicine necessitated a shift where the protection of the “human in the loop” became as vital as the encryption of the data itself. Strategic actions emphasized that a culture of skepticism and continuous education was the only way to ensure patient confidentiality remained uncompromised.