The modern automobile has rapidly transitioned from a traditional mechanical conveyance into a highly sophisticated, software-defined ecosystem that functions more like a mobile computing platform than a simple machine. This shift toward the “smartphone on wheels” model has introduced a suite of features that were once the province of science fiction, such as real-time telematics, cloud-based navigation, and integrated mobile application suites. However, as vehicles become permanently connected internet devices, they also inherit the complex vulnerabilities associated with global networking. This evolution mirrors the early challenges faced by the personal computer industry, where the drive for rapid innovation and user convenience often outpaced the implementation of rigorous security architectures. Today, the automotive sector finds itself in a critical period where the physical safety of passengers is inextricably linked to the integrity of millions of lines of code that govern everything from infotainment to powertrain control.
Identifying the Dual Nature of Cyber Threats
Risks to Physical Control and Functional Systems
The primary concern for many observers remains the theoretical ability of a malicious actor to remotely manipulate critical vehicle functions such as steering, braking, or engine performance. Early experimental demonstrations by security researchers proved that it was possible to bypass internal network protections to send unauthorized commands to the Electronic Control Units (ECUs) that manage a car’s physical behavior. While these high-profile scenarios require significant technical expertise and specific conditions to execute, they have fundamentally changed how manufacturers approach safety. Modern vehicle architectures now utilize segmented networks to isolate comfort features from safety-critical systems, ensuring that a breach in the Wi-Fi hotspot does not grant access to the braking module. This “defense-in-depth” strategy is essential because as more vehicles move toward drive-by-wire technology, the reliance on digital signals over mechanical linkages makes the consequences of a successful hack potentially life-threatening.
Furthermore, the threat of functional disruption extends beyond individual vehicle takeovers to the broader impact on public infrastructure. If a vulnerability were discovered within a standardized communication protocol used across multiple brands, it could theoretically allow for large-scale disruptions, such as stalling hundreds of vehicles simultaneously in a concentrated geographic area. This collective risk has led to the development of mandatory global standards, which require manufacturers to implement rigorous monitoring and response capabilities throughout the entire lifecycle of the vehicle. These protocols are designed to detect anomalous behavior on the internal Controller Area Network (CAN) bus, which serves as the central nervous system of the automobile. By identifying and neutralizing unauthorized messages in real-time, these systems provide a critical layer of protection against the most severe forms of digital interference that could lead to physical accidents on public roads.
The Growing Crisis of Data Privacy and Identity Theft
While functional hijacking captures headlines, a more pervasive and immediate threat is the systematic harvesting of sensitive personal data stored within vehicle infotainment systems. These units act as digital repositories, frequently synchronizing with owner smartphones to store call logs, text messages, private contact lists, and granular location history. This information is a goldmine for identity thieves and corporate espionage, as it provides a detailed map of an individual’s daily routines, professional networks, and personal habits. Many drivers are unaware that their vehicle may be recording and uploading driving telemetry, voice commands, and even biometric data to manufacturer servers. Without robust encryption and clear user controls, this data remains vulnerable to interception during transmission or through unauthorized access to the vehicle’s hardware, especially when owners fail to clear their profiles before a sale.
The danger of data exploitation is particularly acute in the secondary market, where used vehicles are often sold with the previous owner’s digital footprint still fully intact. Investigations into recently sold vehicles have revealed that a significant number of cars still contain active links to the previous owner’s home garage door openers, cloud storage accounts, and saved navigation destinations. This lack of digital hygiene creates a significant security gap, as a new buyer or a malicious actor could easily gain access to the private life of a stranger. To combat this, some manufacturers are introducing “privacy modes” and simplified factory reset procedures, yet the burden remains largely on the consumer to understand the scope of information being collected. As vehicles become more integrated with financial payment systems for fuel or tolls, the risk of financial fraud through a compromised dashboard interface is becoming an urgent priority for the global automotive industry.
Beyond the Dashboard: Systemic and Future Risks
Vulnerabilities in the Global Automotive Supply Chain
The security of a modern vehicle is not determined solely by the final manufacturer but is the cumulative result of a vast, interconnected global supply chain. Each car contains components from dozens of different third-party vendors, many of whom provide proprietary software and firmware that the primary automaker may not fully control or even have the ability to audit. A single vulnerability in a widely used communication chip or a specific library of code can compromise millions of vehicles across different brands simultaneously. Recent history has shown that ransomware attacks on Tier 1 and Tier 2 suppliers can effectively paralyze the entire production process of a major manufacturer, causing billions of dollars in losses. This systemic fragility highlights the fact that cybersecurity is not just a feature of the car itself, but a requirement for the entire industrial infrastructure that designs, builds, and maintains it over time.
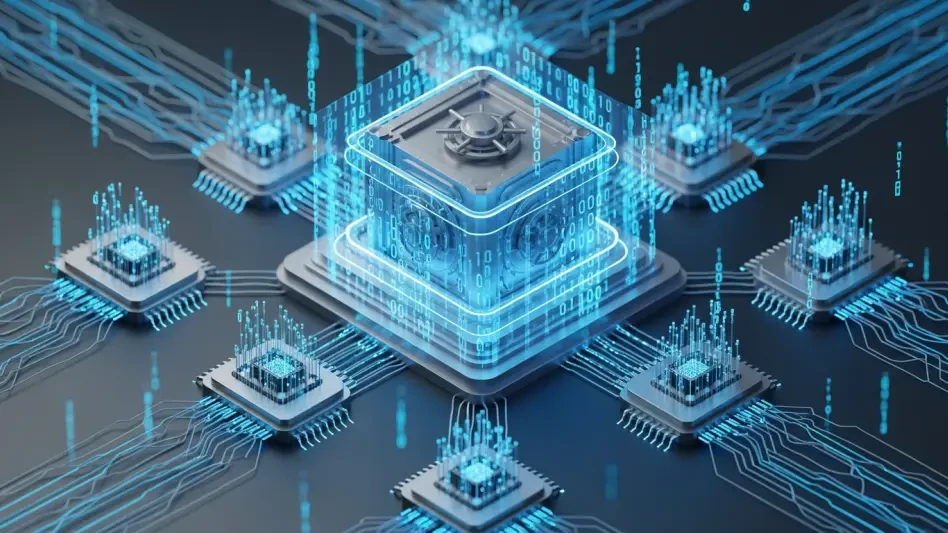
Moreover, the increasing reliance on cloud-based services for remote diagnostics and over-the-air (OTA) updates introduces new vectors for enterprise-level breaches. If a manufacturer’s central update server were compromised, an attacker could potentially distribute malicious code to an entire fleet of vehicles under the guise of a legitimate system patch. This “supply chain injection” is one of the most sophisticated threats facing the industry today, as it bypasses local security measures by exploiting the inherent trust between the vehicle and the manufacturer. Consequently, automakers are now implementing multi-stage verification processes and cryptographically signed firmware to ensure that only authorized code can be executed. This shift toward a “zero-trust” architecture within the production and maintenance cycle is a necessary response to the reality that a breach anywhere in the network can have catastrophic consequences for the security of the end-user.
Challenges for Semi-Autonomous and Autonomous Fleets
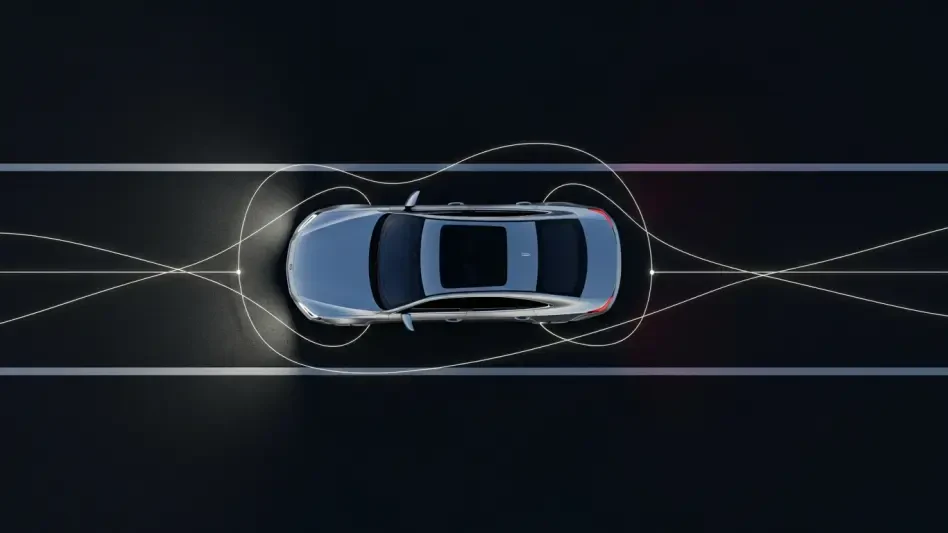
As the industry transitions from human-operated vehicles to semi-autonomous and fully autonomous systems, the complexity and severity of cyber threats increase exponentially. These advanced vehicles rely on a constant stream of data from cameras, radar, lidar, and V2X (Vehicle-to-Everything) communication systems to make split-second driving decisions. A malicious actor could theoretically manipulate the sensor data or the external signals the car receives, leading the vehicle to misinterpret its environment or follow an unsafe path. Unlike a manual car, where a driver can physically intervene, an autonomous system may not have a mechanical backup if its logic is compromised. This makes the integrity of the sensor fusion algorithms and the security of the communication channels a paramount concern for regulators and engineers alike, as the “driver” is now a piece of software that must be protected from external interference.
Furthermore, the rise of autonomous ride-hailing fleets creates a centralized target for attackers who are looking to cause maximum disruption for financial or political gain. A fleet management system that coordinates the movement of thousands of vehicles represents a single point of failure; if compromised, it could be used to gridlock an entire city or redirect vehicles to specific locations. The incentive for cybercriminals to target these centralized networks is much higher than the incentive to hack a single private car, as the potential for extortion or large-scale chaos is significantly greater. To mitigate these risks, future autonomous networks must be built on decentralized protocols that prevent any single breach from affecting the entire fleet. This involves a fundamental rethinking of how vehicles communicate with each other and the infrastructure around them, moving away from vulnerable central hubs toward more resilient, distributed security models.
Proactive Defenses and Consumer Responsibility
Manufacturer Strategies and Technical Guardrails
Automotive manufacturers have responded to these growing digital threats by establishing dedicated cybersecurity centers and partnering with specialized firms to conduct “red team” penetration testing. These facilities, such as those operated by major brands in tech hubs like Frankfurt and Silicon Valley, are designed to find and fix vulnerabilities before a vehicle ever reaches the showroom floor. One of the most effective tools in this defensive arsenal is the implementation of over-the-air (OTA) update capabilities, which allow manufacturers to push security patches to vehicles in real-time. This mirrors the update cycles of modern smartphones and ensures that when a new exploit is discovered in the wild, it can be neutralized across the entire fleet within hours. This proactive approach significantly shortens the window of opportunity for attackers and ensures that the vehicle’s software remains resilient against the latest threats.
In addition to software patches, engineers are building hardware-level security into the vehicles, such as Secure Hardware Extensions (SHE) and Hardware Security Modules (HSM). These dedicated chips are designed to handle cryptographic keys and secure boot processes, ensuring that the vehicle’s core operating system cannot be tampered with or replaced by unauthorized software. By moving these critical functions into a dedicated, tamper-resistant environment, manufacturers create a solid foundation for all other security layers. This structural approach is complemented by the use of machine learning algorithms that monitor the vehicle’s data traffic for signs of intrusion. These AI-driven systems can recognize the “fingerprint” of a cyberattack—such as an unusual frequency of messages on the internal network—and automatically trigger a safe mode that limits the vehicle’s connectivity while maintaining essential driving functions, providing a final safety net for the driver.
Essential Security Practices for the Modern Driver
While manufacturers provide the technical framework for a secure vehicle, the ultimate responsibility for data protection and operational safety often rested with the individual owner. Drivers must adopt a mindset of digital hygiene that treats their car with the same caution as a laptop or a mobile phone. This includes the regular installation of all manufacturer software updates, as these often contain critical fixes for newly discovered security holes. Neglecting these updates is equivalent to leaving a computer’s operating system unpatched, leaving the vehicle open to known exploits that have already been addressed by the factory. Furthermore, users should be extremely cautious about what third-party devices they plug into their car’s physical ports, such as the OBD-II diagnostic port or USB connections, as these can serve as entry points for malware or unauthorized data extraction tools.
Beyond software maintenance, physical security measures have proven to be an effective deterrent against modern car theft techniques like relay attacks. These attacks involve intercepting the signal from a key fob to trick the car into thinking the owner is nearby, allowing thieves to unlock and start the vehicle without a physical key. Using signal-blocking Faraday pouches for key storage was a simple but effective countermeasure that many owners adopted to protect their property. Additionally, when it came time to transfer ownership, savvy drivers performed comprehensive factory resets and manually revoked all digital permissions for connected apps and streaming services. By taking these proactive steps, consumers ensured that their transition into the era of connected mobility was defined by convenience rather than vulnerability. Ultimately, the successful securing of the automotive landscape was achieved through a combination of industrial vigilance and informed personal responsibility.