Hamas-Linked Group Escalates Mideast Cyber Espionage Campaign
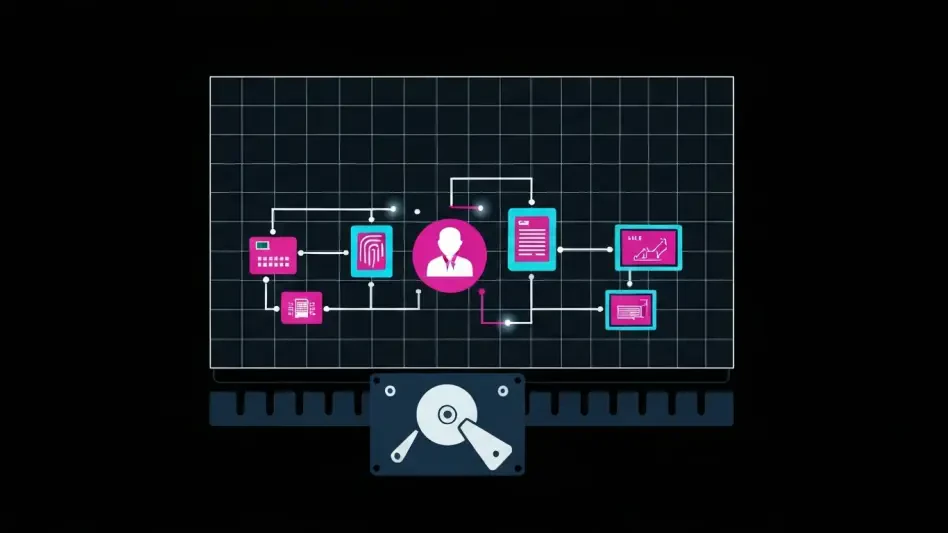
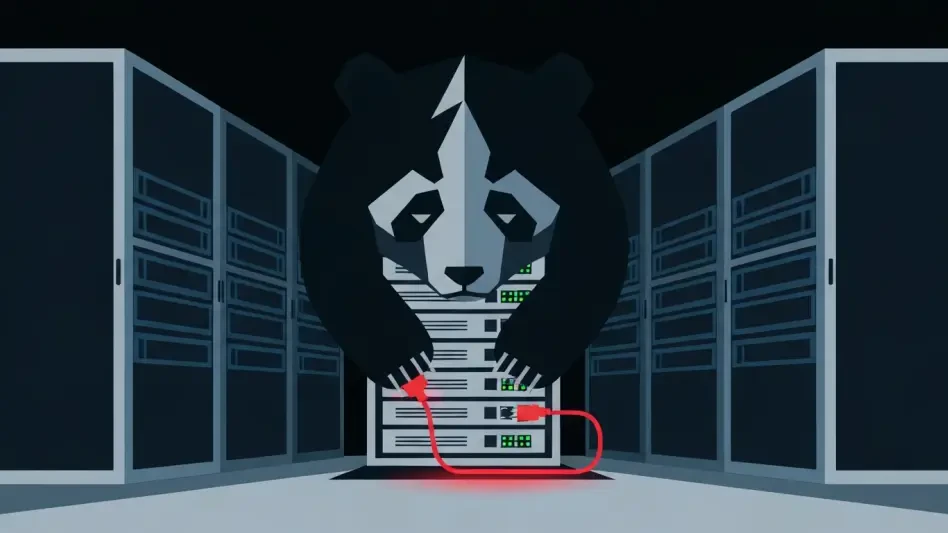
In a significant escalation of regional cyber conflict, a detailed analysis has revealed that a Hamas-linked cyber espionage group, known as Ashen Lepus, has intensified its operations targeting governmental and diplomatic entities across the Middle...