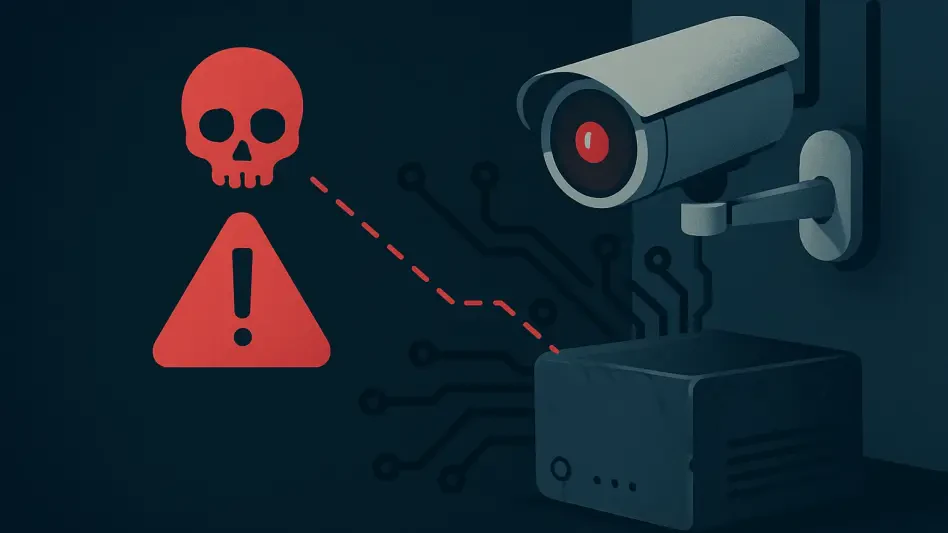
How Can Pakistan Combat Rising Phishing Cyberattacks?
In a digital landscape increasingly fraught with danger, Pakistan faces an alarming surge in phishing cyberattacks that exploit unsuspecting citizens through deceptive SMS, WhatsApp messages, and fraudulent phone calls, leading to significant financi...
Read More