How Will This Merger Change Security Training?
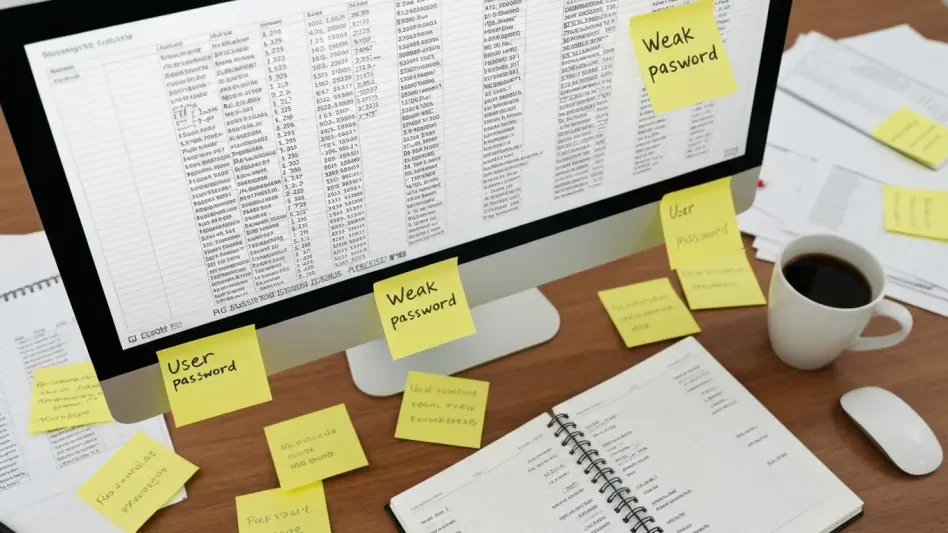
In an industry where human error remains a primary vector for cyberattacks, the landscape of security awareness training is undergoing a significant transformation as human risk management firm MetaCompliance has officially announced its acquisition...
Read More