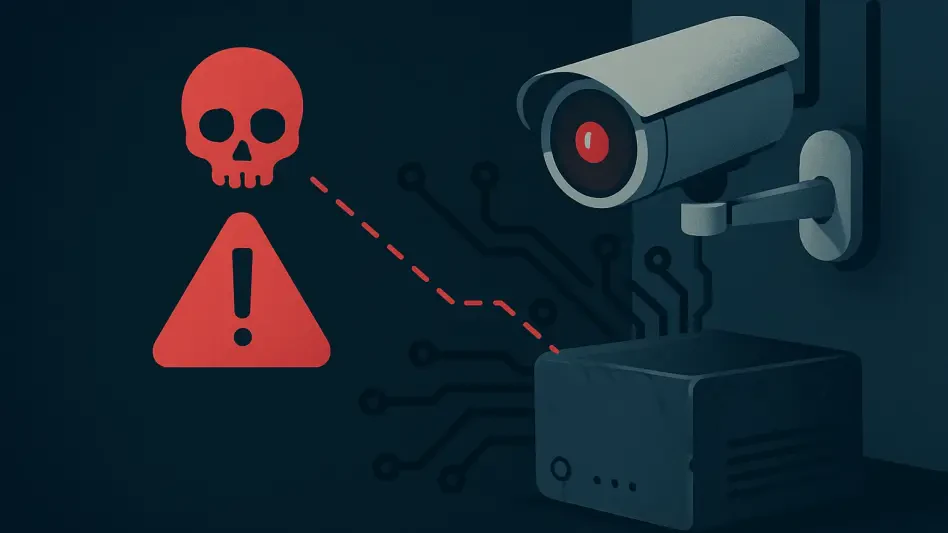
Cybercriminals Shift from Encryption to Pure Extortion
A meticulously built fortress of data backups, once the gold standard of cyber defense, is now proving to be an inadequate shield against a new and insidious form of digital siege.
Feature Article Read More