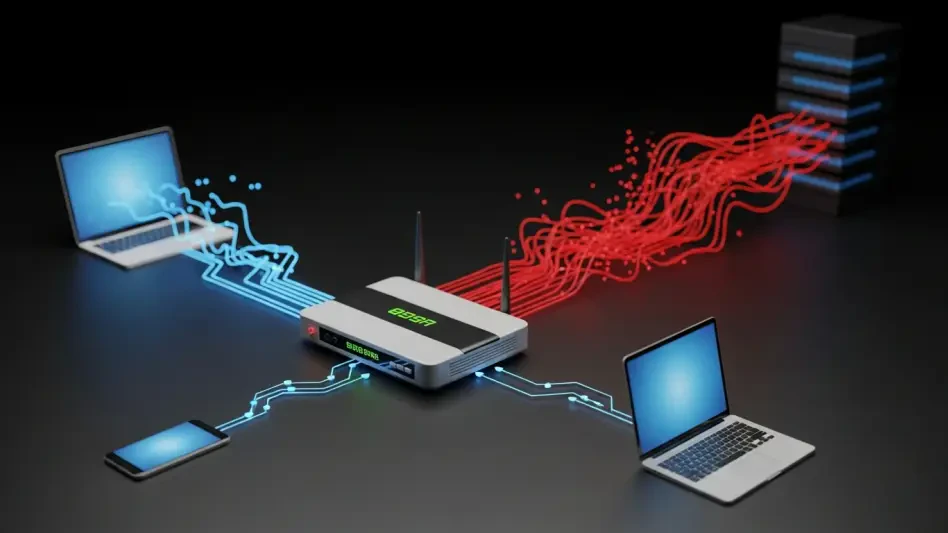
Global Campaign Hijacks DNS on Outdated Routers
An insidious threat is quietly turning millions of home networks into unwitting participants in a global scheme, redirecting personal web traffic through a shadowy infrastructure for criminal profit.
Research Summary Read More