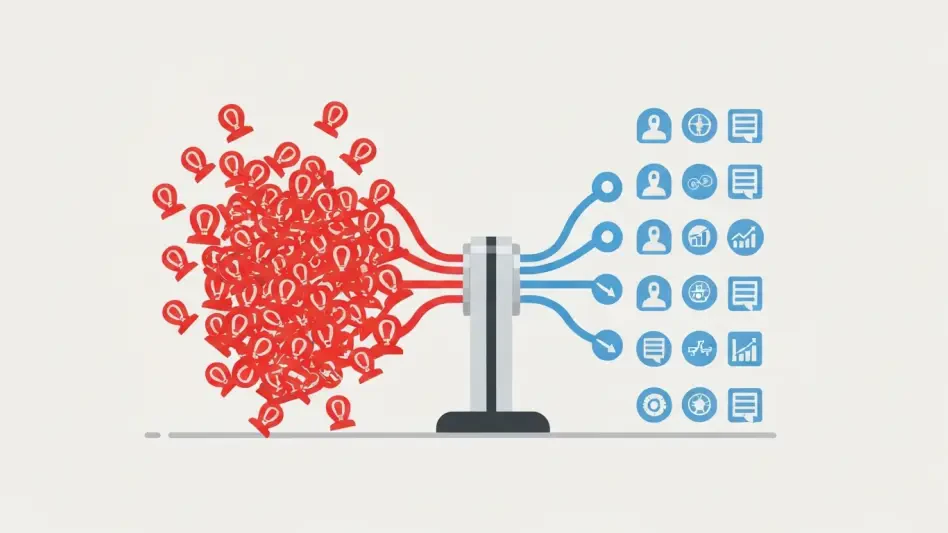
Is Your Salesforce Your Biggest Attack Surface?
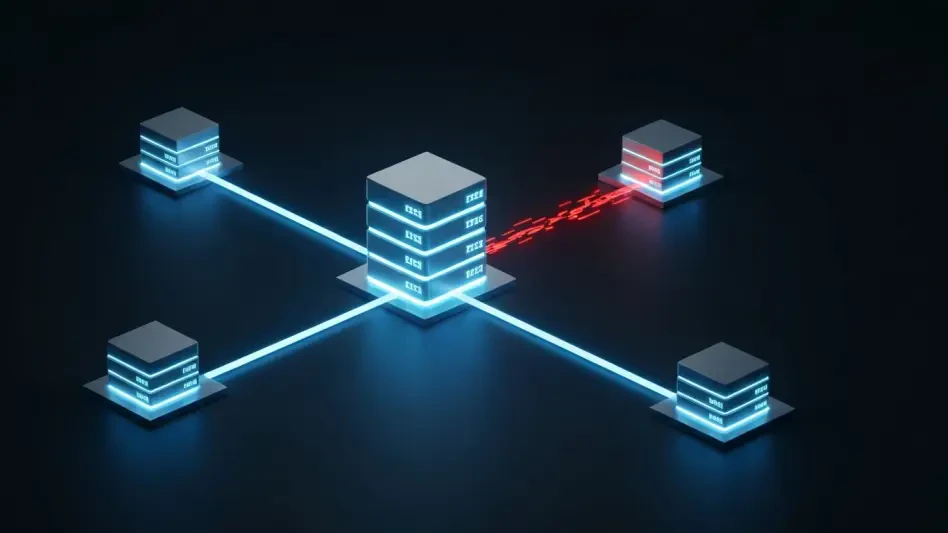
The critical data underpinning your company's most sensitive operations, from M&A contracts to patient health records, might be residing in a digital environment that your security team has never systematically audited.
Feature Article