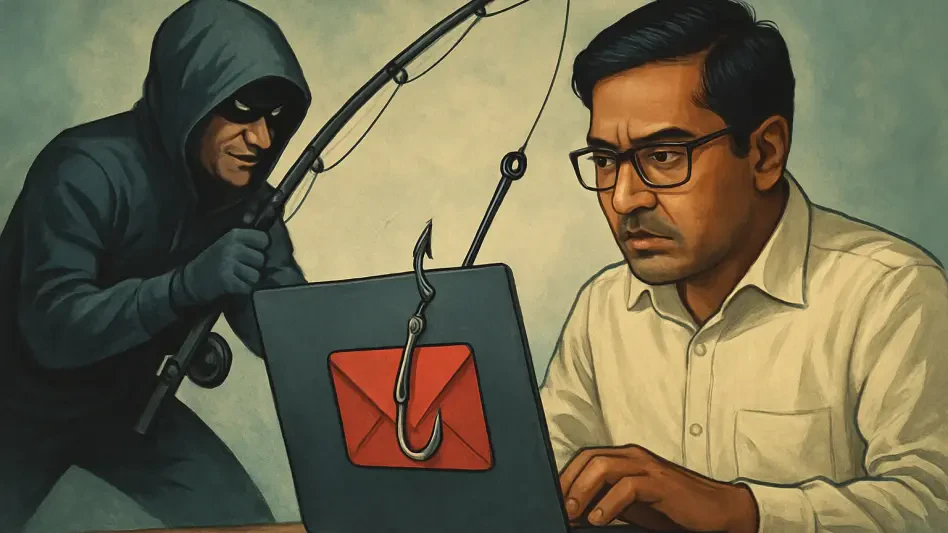
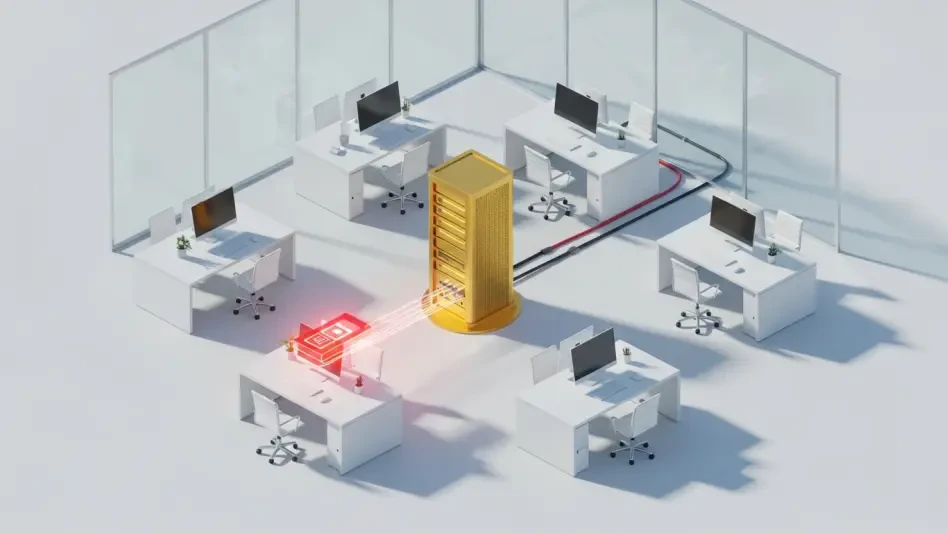
How Can We Modernize Insider Threat Protections Now?
In a world where national security systems are under constant siege from both external and internal dangers, the specter of insider threats looms larger than ever before, demanding urgent attention.
Read More