Trend Analysis: Global Ransomware Evolution
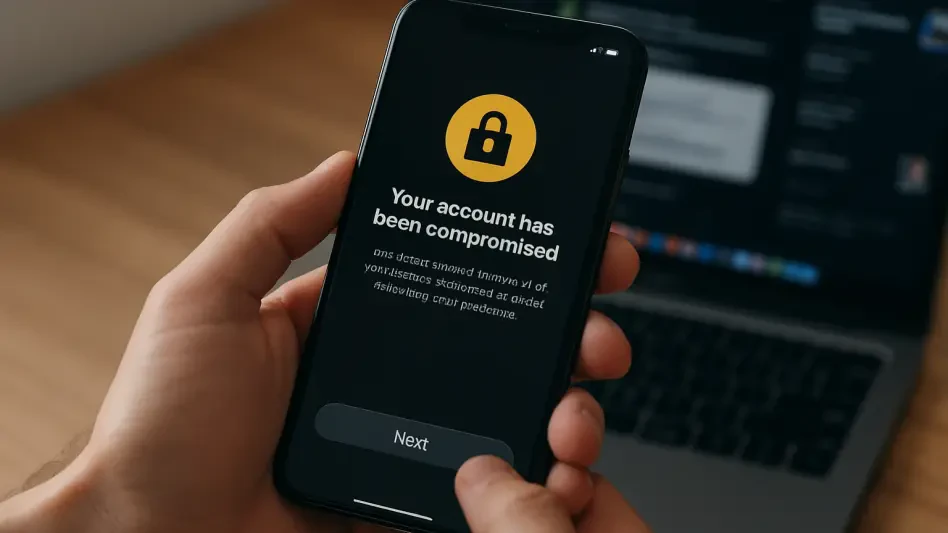
Modern cyber extortionists have abandoned the chaotic methods of the past in favor of highly calculated, sector-specific strikes that transform stolen data into the primary weapon of digital warfare. As…
Read More