Is EU Cybersecurity Maturity Keeping Up With Rising Risks?
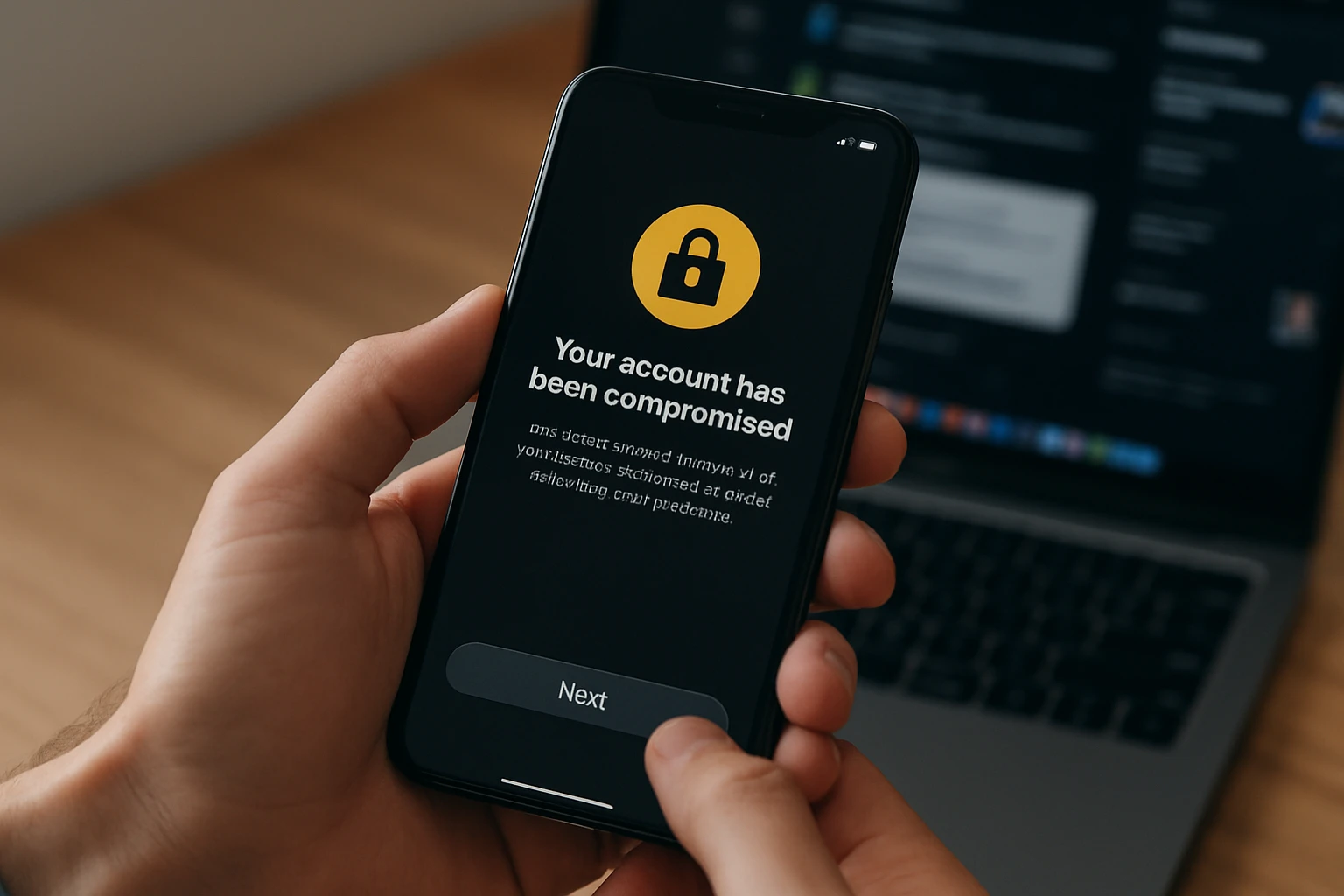
The digital architecture of the European Union currently stands at a crossroads where the velocity of technological innovation often outpaces the development of defensive measures. As the 2026 ENISA NIS360…
Read More