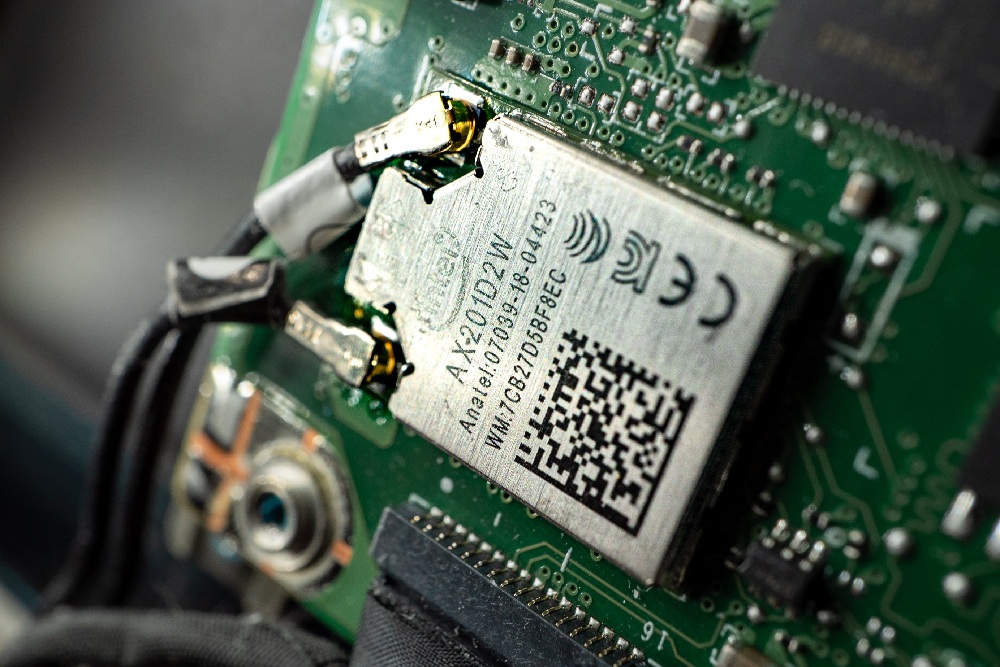
The low-power Wi-Fi module is designed for use in embedded devices, and is being used in a broad range of industries, including automotive, agriculture, energy, healthcare, industrial, and security.
The RTL8195A chip supports WEP, WPA and WPA2 authentication modes, and Vdoo discovered that the WPA2 handshake mechanism is prone to stack overflow and out-of-bounds read bugs.
Tracked as CVE-2020-9395, the most severe of the flaws is a remotely exploitable stack overflow that could lead to a complete takeover of the module and the device’s wireless communications. The vulnerability can be exploited by an attacker in the proximity of a vulnerable system, even if they don’t know the Wi-Fi network password (Pre-Shared-Key, or PSK).